Microsoft updates it’s bug bounties:
Author: hucktech
Intel announces Core-X series
Intel introduced the new Intel® Core™ X-series processor family on May 30, 2017. Intel’s most scalable, accessible and powerful desktop platform ever, it includes the new Intel® Core™ i9 processor brand and the Intel® Core™ i9 Extreme Edition processor – the first consumer desktop CPU with 18 cores and 36 threads of power. The company also introduced the Intel® X299, which adds even more I/O and overclocking capabilities.
https://newsroom.intel.com/editorials/new-intel-core-x-series-processors-scale-accessibility-and-performance-go-extreme/
https://newsroom.intel.com/press-kits/intel-core-x-series-processors/
http://www.intel.com/content/www/us/en/products/processors/core/x-series.html
https://newsroom.intel.com/tag/intel-core-x-series/
NIST SP 800-193: Platform Firmware Resiliency Guidelines
I thought I got all the appropriate NIST announcements, but missed this, found it in Vincent’s recent blog post:
http://vzimmer.blogspot.com/2017/05/uefi-and-security-postings.html
Very exciting to see this NIST document!
Draft NIST Special Publication 800-193
Platform Firmware Resiliency Guidelines
Andrew Regenscheid
This document provides technical guidelines and recommendations supporting resiliency of platform firmware and data against potentially destructive attacks. The platform is a collection of fundamental hardware and firmware components needed to boot and operate a system. A successful attack on platform firmware could render a system inoperable, perhaps permanently or requiring reprogramming by the original manufacturer, resulting in significant disruptions to users. The technical guidelines in this document promote resiliency in the platform by describing security mechanisms for protecting the platform against unauthorized changes, detecting unauthorized changes that occur, and recovery from attacks rapidly and securely. Implementers, including Original Equipment Manufacturers (OEMs) and component/device suppliers, can use these guidelines to build stronger security mechanisms into platforms. System administrators, security professionals, and users can use this document to guide procurement strategies and priorities for future systems.
http://csrc.nist.gov/publications/PubsDrafts.html#SP-800-193
Intel SSD Toolbox EoP vulnerability
Intel® Solid State Drive Toolbox™ Escalation of Privilege Vulnerability
Intel ID: INTEL-SA-00074
Product family: Intel® Solid State Drive Toolbox™
Impact of vulnerability: Elevation of Privilege
Severity rating: Important
Original release: May 30, 2017
There is an escalation of privilege vulnerability in the Intel® Solid State Drive Toolbox™ versions before 3.4.5 which allow a local administrative attacker to load and execute arbitrary code.[…]
https://security-center.intel.com/advisory.aspx?intelid=INTEL-SA-00074&languageid=en-fr
TGBL: Text & Graphics BIOS library
TGBL: Text & Graphics BIOS library
A set of functions & macros helping you write less and write fast.
ARM assembly basics, part 1
Introduction to ARM Assembly Basics
Welcome to this tutorial series on ARM assembly basics. This is the preparation for the followup tutorial series on ARM exploit development (not published yet). Before we can dive into creating ARM shellcode and build ROP chains, we need to cover some ARM Assembly basics first. The following topics will be covered step by step:
ARM Assembly Basics Tutorial Series:
Part 1: Introduction to ARM Assembly
Part 2: Data Types Registers
Part 3: ARM Instruction Set
Part 4: Memory Instructions: Loading and Storing Data
Part 5: Load and Store Multiple
Part 6: Conditional Execution and Branching
Part 7: Stack and Functions
chip hacks will become more popular
Roger A. Grimes has an article in CSO entitled “6 reasons chip hacks will become more popular”.
SimpleSvm: hypervisor for AMD Windows systems
SimpleSvm is a minimalistic educational hypervisor for Windows on AMD processors. It aims to provide small and explanational code to use Secure Virtual Machine (SVM), the AMD version of Intel VT-x, with Nested Page Tables (NPT) from a windows driver. SimpleSvm is inspired by SimpleVisor, an Intel x64/EM64T VT-x specific hypervisor for Windows, written by Alex Ionescu.
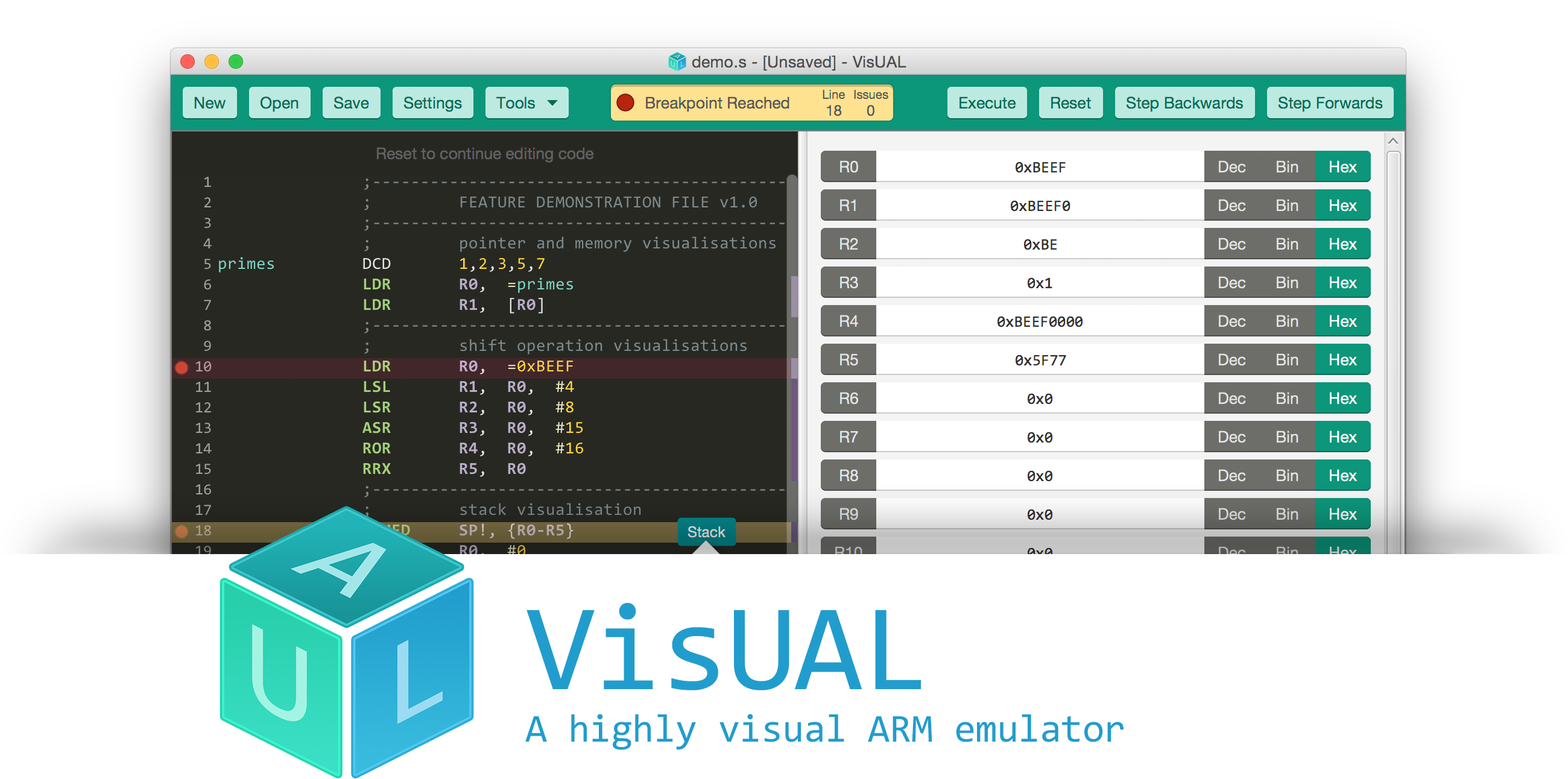
VisUAL: ARM emulator
Created by Salman Arif, 2015, Imperial College London. Last release 2015.
Vape Pens: source of USB attacks
https://twitter.com/FourOctets/status/867764655954866176
If you have a vaping device, make sure it supports Verified/Secure/Trusted/etc Boot. 🙂
[…]Take this as the weirdest example yet that you should never plug random devices into your USB ports. […] While FourOctets has no ill-intent, it is easy to imagine someone less scrupulous loading a computer with something not quite as funny. Like, say, a keylogger. Or ransomware.[…]
http://mashable.com/2017/05/26/vaping-digital-security-virus-usb/#iAjGmK3E0mqd
A related presentation, as suggested from a poster in the above twitter thread:
Holy smokes, how to vape yourself to root
Ross Bevington
Abstract: We all know that smoking is bad for your health, but what about you or your organisations security? I’ll show you that an eCig isn’t just a glorified smoke machine but a low power, battery operated, exploitation platform. I’ll show you how easy it is to decrypt the firmware, write your own functionality and use this to pwn some systems. Turning your eCig into everything from a keyboard to a USB stick. On the way we’ll do a bit of reverse engineering, write a bit of code and show how you can do most of this on a shoe string budget. Looking for ways to defend against attacks like this? I have some options. Consider this talk if you want another reason to ban smoking at your organisation.
HardwareSecurity.Training
Does ‘power trio’ apply to training companies, as well as rock bands? 🙂
https://twitter.com/nedos/status/868089302646960129
“Combined, we have over 25 years of experience teaching hardware security trainings and we have taught hundreds of classes. We have helped leading tech companies build their security teams and taught thousands of hardware security engineers the skills necessary for their day to day work. Our unique experience is unparalleled in the industry.”
https://twitter.com/nedos/status/868096436210212864
https://hardwaresecurity.training/trainings/
https://hardwaresecurity.training/
http://www.grandideastudio.com/
https://www.securinghardware.com/
Nintendo 3DS
A few links to Nintendo 3DS firmware. The first tweet below hints of Nintendo having a response (ban?) to custom firmware.
Nintendo’s Next Ban Wave is Targeting Hacked 3DS’s, Here’s Everything We Know
https://twitter.com/aquamarinedoto/status/867832446099668992
sighax is a BootROM exploit (revealed at 33c3) for the Nintendo 3DS/2DS/New3DS. It exploits a vulnerability in the RSA signature parser and allows you to run fake-signed firmware on any console.
“Keyshuffling Attack for Persistent Early Code Execution in the Nintendo 3DS Secure Bootchain”
https://github.com/Plailect/keyshuffling
A complete guide to developer 3DS custom firmware, from stock to boot9strap.
https://github.com/Plailect/devGuide
https://github.com/Plailect/Guide
A tool to parse, extract, and builds 3DS firmware files
https://github.com/TuxSH/firmtool
Luma3DS is a program to patch the system software of (New) Nintendo 3DS handheld consoles “on the fly”, adding features (such as per-game language settings and debugging capabilities for developers) and removing restrictions enforced by Nintendo (such as the region lock). It also allows you to run unauthorized (“homebrew”) content by removing signature checks. To use it, you will need a console capable of running homebrew software on the ARM9 processor. We recommend Plailect’s guide for details on how to get your system ready.
https://github.com/AuroraWright/Luma3DS
AGESA update info from AMD
[…]Beginning this month, as we promised to you, we began beta testing a new AGESA (v1.0.0.6) that is largely focused on aiding the stability of overclocked DRAM (>DDR4-2667). We are now at the point where that testing can begin transitioning into release candidate and/or production BIOSes for you to download. Depending on the QA/testing practices of your motherboard vendor, full BIOSes based on this code could be available for your motherboard starting in mid to late June. Some customers may already be in luck, however, as there are motherboards—like my Gigabyte GA-AX370-Gaming5 and ASUS Crosshair VI—that already have public betas.
[…]
If you’re the kind of user that just needs (or loves!) virtualization every day, then AGESA 1.0.0.6-based firmware will be a blessing for you thanks to fresh support for PCI Express Access Control Services (ACS). ACS primarily enables support for manual assignment of PCIe graphics cards within logical containers called “IOMMU groups.” The hardware resources of an IOMMU group can then be dedicated to a virtual machine. This capability is especially useful for users that want 3D-accelerated graphics inside a virtual machine. With ACS support, it is possible to split a 2-GPU system such that a host Linux® OS and a Windows VM both have a dedicated graphics cards. The virtual machine can access all the capabilities of the dedicated GPU, and run games inside the virtual machine at near-native performance.[…]
https://community.amd.com/community/gaming/blog/2017/05/25/community-update-4-lets-talk-dram
http://www.tomshardware.com/news/amd-agesa-firmware-update-motherboard,34525.html
DMTF updates MCTP SMBus/I2C Transport Binding spec
DMTF Releases Updated MCTP SMBus/I2C Transport Binding Specification
The DMTF’s Platform Management Components Intercommunication (PMCI) Working Group defines standards to address “inside the box” communication and functional interfaces between the components of the platform management subsystem (e.g., management controllers, managed devices, etc.). PMCI’s Management Component Transport Protocol (MCTP) over SMBus/I2C Transport Binding Specification is now available in version 1.1.0 . This specification addresses how MCTP packets are delivered over a physical SMBus or I2C medium using SMBus transactions. It defines how physical addresses are used, how fixed addresses are accommodated, how physical address assignment is accomplished for hot-plug or other devices that require dynamic physical address assignment, and how MCTP support is discovered. In addition, timing specifications for bus and MCTP control operations are included, and a “fairness” protocol is defined for the purpose of avoiding deadlock and starvation/lockout situations among MCTP endpoints. The binding has been designed to be able to share the same bus as devices communicating using earlier SMBus/I2C management protocols, such as Alert Standard Format (ASF) and Intelligent Platform Management (IPMI), and with vendor-specific devices using SMBus/I2C protocols. The specification also allows a given device to incorporate non-MCTP SMBus functions alongside MCTP.
Analyzing ECU firmware
How They Did It: An Analysis of Emission Defeat Devices in Modern Automobiles
Modern vehicles are required to comply with a range of environmental regulations limiting the level of emissions for various greenhouse gases, toxins and particulate matter. To ensure compliance, regulators test vehicles in controlled settings and empirically measure their emissions at the tailpipe. However, the black box nature of this testing and the standardization of its forms have created an opportunity for evasion. Using modern electronic engine controllers, manufacturers can pro- grammatically infer when a car is undergoing an emission test and alter the behavior of the vehicle to comply with emission standards, while exceeding them during normal driving in favor of improved performance. While the use of such a defeat device by Volkswagen has brought the issue of emissions cheating to the public’s attention, there have been few details about the precise nature of the defeat device, how it came to be, and its effect on vehicle behavior. In this paper, we present our analysis of two families of software defeat devices for diesel engines: one used by the Volkswagen Group to pass emissions tests in the US and Europe, and a second that we have found in Fiat Chrysler Automobiles. To carry out this analysis, we developed new static analysis firmware forensics techniques necessary to automatically identify known defeat devices and confirm their function. We tested about 900 firmware images and were able to detect a potential defeat device in more than 400 firmware images spanning eight years. We describe the precise conditions used by the firmware to detect a test cycle and how it affects engine behavior. This work frames the technical challenges faced by regulators going forward and highlights the important research agenda in providing focused software assurance in the presence of adversarial manufacturers.
USBProxy
https://twitter.com/typhoonfilsy/status/867912807659872256
“A USB man in the middle device using USB On-The-Go, libUSB and gadgetFS”
https://github.com/dominicgs/USBProxy
See-also:
https://greatscottgadgets.com/greatfet/
Intel ATR releases UEFI firmware training materials!
Good news: the Intel Advanced Threat Research (ATR) team has release some of their UEFI security training materials!
This repository contains materials for a hands-on training ‘Security of BIOS/UEFI System Firmware from Attacker and Defender Perspectives’. A variety of attacks targeting system firmware have been discussed publicly, drawing attention to the pre-boot and firmware components of the platform such as BIOS and SMM, OS loaders and secure booting. This training will detail and organize objectives, attack vectors, vulnerabilities and exploits against various types of system firmware such as legacy BIOS, SMI handlers and UEFI based firmware, mitigations as well as tools and methods available to analyze security of such firmware components. It will also detail protections available in hardware and in firmware such as Secure Boot implemented by modern operating systems against bootkits. The training includes theoretical material describing a structured approach to system firmware security analysis and mitigations as well as many hands-on exercises to test system firmware for vulnerabilities. After the training you should have basic understanding of platform hardware components and various types of system firmware, security objectives and attacks against system firmware, mitigations available in hardware and firmware. You should be able to apply this knowledge in practice to identify vulnerabilities in BIOS and perform forensic analysis of the firmware.
0 Introduction to Firmware Security
1 BIOS and UEFI Firmware Fundamentals
2 Bootkits and UEFI Secure Boot
3 Hands-On Platform Hardware and Firmware
4 System Firmware Attack Vectors
5 Hands-On EFI Environment
6 Mitigations
7 System Firmware Forensics
N Miscellaneous Materials
https://github.com/advanced-threat-research/firmware-security-training
FWTS 17.05.00 released
Ivan Hu of Canonical announced the 17.05.00 release of FWTS.
New Features:
* Support SMBIOS 3.1.1 tests
* dmi: dmicheck: check new offset in spec 3.11
* dmi: dmicheck: check reserved bits of Type 7 offset 0x5
* dmi: dmicheck: check reserved bits of Type 7 offset 0xd
* dmi: dmicheck: add a function to verify reserved bits
* dmi: dmicheck: add a helper function to check word min/max value
* dmi: dmicheck: check pci(e) slot and segment, bus and dev/func
* dmi: dmicheck: check reserved bits of offset 0x5 in type 13
* dmi: dmicheck: add a helper function to check a reserved offset
* dmi: dmicheck: check reserved bits in type 15 & type 17
* dmi: dmicheck: check reserved fields in type 22, 23, 30, 32, 38 and 39
* dmi: dmicheck: add 64-bit integer to dmi_reserved_bits_check
* dmi: dmicheck: add checks for new type 43
* dmi: dmicheck: check reserved bits in Type 0
* fwts/opal: Power management DT Validation tests.
* fwts/opal: Reserved memory DT validation tests.
* Add snapcraft rules to build a fwts snap
See the list of bugfixes in the full announcement.
http://fwts.ubuntu.com/release/fwts-V17.05.00.tar.gz
https://launchpad.net/~firmware-testing-team/+archive/ubuntu/ppa-fwts-stable
https://wiki.ubuntu.com/FirmwareTestSuite/ReleaseNotes/17.05.00
https://launchpad.net/ubuntu/+source/fwts
NEZHA fuzzer open-sourced
NEZHA is an evolutionary-based efficient and domain-independent differential testing framework developed at Columbia University. NEZHA exploits the behavioral asymmetries between multiple test programs to focus on inputs that are more likely to trigger semantic bugs. NEZHA features several runtime diversity-promoting metrics used to generate inputs for multi-app differential testing.[…]
initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line Injection
initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line Injection
By Roee Hay (@roeehay)
In the May 2017 Android Security Bulletin, Google released a patch to a critical and unique vulnerability CVE-2016-10277 in the Nexus 6 bootloader we had found and responsibly disclosed. By exploiting the vulnerability, a physical adversary or one with authorized-ADB/fastboot USB access to the (bootloader-locked) device (such as PC malware awaiting for an ADB-authorized developer’s device to be hooked via USB) could break the Secure/Verified Boot mechanism, allowing him to gain unrestricted root privileges, and completely own the user space (which may also lead much more), by loading a tampered or malicious initramfs image. Moreover, exploitation does not lead to a factory reset hence user data remains intact (and still encrypted). It should be noted that we do not demonstrate an untethered attack. During this research we also uncovered a 18-year-old Linux Kernel bug (not affecting Nexus 6 and probably does not affect any Android device): CVE-2017-1000363[…]

You must be logged in to post a comment.