A new set of UEFI tools for interacting with the TPM:
https://github.com/HPBirdTW/ShellTpm20CmdAct
See-also:
A new set of UEFI tools for interacting with the TPM:
https://github.com/HPBirdTW/ShellTpm20CmdAct
See-also:
BitLeaker is a new tool for extracting the VMK and mounting a BitLocker-locked partition. BitLeaker uses the TPM vulnerability, CVE-2018-6622 for a discrete TPM and related vulnerability for a firmware TPM. They are related to the S3 sleeping state of Advanced Configuration and Power Interface (ACPI) and can reset the TPMs. If you want the detailed information about CVE-2018-6622 and a vulnerability checking tool, please read our USENIX paper, A Bad Dream: Subverting Trusted Platform Module While You Are Sleeping and Black Hat Asia presentation, Finally, I Can Sleep Tonight: Catching Sleep Mode Vulnerabilities of the TPM with Napper.
There is a new web site with multiple TPM resources, many things to see. And a physical event, if you are based in Germany.
Finally, I Can Sleep Tonight: Catching Sleep Mode Vulnerabilities of the TPM with the Napper
Seunghun Han | Senior Security Researcher, National Security Research Institute of South Korea
Jun-Hyeok Park | Senior Security Researcher, National Security Research Institute of South Korea
[…]In this talk, we present two vulnerabilities, CVE-2017-16837 and CVE-2018-6622. The vulnerabilities we found can subvert the TPM with Advanced Configuration and Power Interface (ACPI). ACPI in PCs, laptops, and servers provide six sleeping states (S0-S5) for reducing power consumption. When the system enters the sleeping state, CPU, device, and RAM are powered off. Since the system powers the components off including security devices, the system should reinitialize them while waking up and this could be the attack surface. We found vulnerabilities on this attack surface without physical access. To mitigate the vulnerabilities, we also present countermeasures and a new tool, “Napper,” to check the vulnerabilities of the TPM. Napper is a bootable USB device based-on Linux, and it has a custom kernel and a vulnerability checking software. When you boot a system with the Napper, it makes your system to take a nap to check the vulnerabilities and to report the result to you.
See-Also:
https://www.usenix.org/conference/usenixsecurity18/presentation/han
A newly completed Trusted Platform Module 2.0 (TPM2) software stack is being introduced, developed to comply with the most recent Trusted Computing Group (TCG) v1.38 specification and work on any TPM2 implementation. Partnering with key players within the domain of Trusted Computing such as Infineon and Fraunhofer SIT, Intel has made large investments in code improvements and new functionality compared to the previous version. This includes the initialization of the TSS Stack development and the SAPI, TCTI and abrmd layer. Based on this development, Infineon and Fraunhofer SIT enabled the support of the Enhanced System API (ESAPI) layer, which is intended to reduce programming complexity and to simplify the use and integration of the TPM.[…]
https://software.intel.com/en-us/blogs/2018/08/29/tpm2-software-stack-open-source
https://github.com/flihp/tpm2-uefi
This is an implementation of a TCTI module for use with the TCG TPM2 Software Stack (TSS2) in the UEFI environment. This library is built as a static archive libtss2-tcti-uefi.a suitable for linking with UEFI applications.
If you want to test software which exploits TPM 2.0 functionality inside the qemu-kvm emulator, this can be challenging because the software stack is still quite new. Here is how I did it.[…]
“This project provides various TPM 2.0 applications running in EFI.”
https://github.com/jiazhang0/efi-tpm2-utils
https://github.com/jiazhang0/efi-tpm2-utils/tree/master/src/efi
AMI has announced support for TPM on Arm®-based systems running AMI’s flagship Aptio® V UEFI Firmware. […] Previously, AMI only provided TPM support for x86 platforms. With the growing need to extend TPM support for additional platforms, AMI has added TPM support for Arm-based systems currently running AMI’s Aptio® V UEFI firmware. The added TPM support for Arm-based systems includes features specifically for the Arm architecture such as TPM driver support within Arm® TrustZone® technology and Linux OS support. The Arm TrustZone TPM Firmware can be accessed by the BIOS and OS via the Command Response Buffer interface using Secure Monitor calls. Other generic features supported by TPM include cryptographic algorithms and measurement of SecureBoot variables.[…]
Microsoft has recently updated (or created?, as I’ve never read it before) this document, showing how to update your TPM firmware.
https://support.microsoft.com/en-us/help/4096377/windows-10-update-security-processor-tpm-firmware
Zero documentation at this point:
https://github.com/Hecmay/fTPM-based-UEFI-remote-attestation
Infineon Technologies Trusted Platform Modules (TPMs), Security Feature Bypass Vulnerability
Document ID: 4015874
Posted Date: 2018-03-20
Last Updated: 2018-03-20
Infineon® Technologies Trusted Platform Modules (TPMs), Security Feature Bypass Vulnerability
NOTICE: The information in this Security Bulletin should be acted upon as soon as possible.
Potential Security Impact: A security vulnerability exists in certain Trusted Platform Module (TPM) firmware. The vulnerability weakens key strength. It is important to note that this is a firmware vulnerability, and not a vulnerability in the operating system or a specific application. Toshiba is working closely with Infineon® to validate their fix and ensure it works across Toshiba’s range of products. Until firmware updates are available, it is recommended that people and companies using Toshiba PCs and devices that incorporate TPMs to take steps to maintain the security of their systems and information.
Toshiba’s TPM Firmware Release Schedule:[…]
Source: Infineon® & Microsoft® Security TechCenter
[…]This tool was primarily developed to manipulate TPM response packets in order to trigger parsing bugs in the host-side TPM drivers. These bugs can be found in the Linux kernel, as well as a variety of bootloaders such as Tboot and Tianocore EDKII. Leveraging these vulnerabilities, an attacker may be able to compromise a host machine after it had successfully booted up into a fully measured and attested state. TPM Genie is also able to man-in-the-middle PCR Extend operations, yielding the ability to undermine most of the stated purposes of a TPM: measured boot, remote attestation, and sealed storage. Normally, attestation or unsealing should fail if an attacker modifies any component of the measured boot process. However, the interposer makes it is possible to spoof these measurements by replacing the the payload associated with the PCR Extend ordinal as it is transmitted across the bus. Additionally, TPM Genie can weaken the Linux hardware random number generator. On some systems, /dev/hwrng is tied into the Trusted Platform Module such that all reads on the character device will actually result in the TPM chip providing the random bytes. In this way, the interposer can subtly alter the platform’s RNG which may impair cryptographic operations on the host. Finally, TPM Genie can be used to simply sniff the bus to capture secrets, such as session data associated with the OIAP and OSAP commands. And with nominal additional engineering effort, TPM Genie should be able to spoof the Endorsement Key, gain control of the AuthData and recalculate the Authorization Session HMAC. (More info on that in my whitepaper. I promise I’ll implement that soon).[…]
https://github.com/nccgroup/TPMGenie

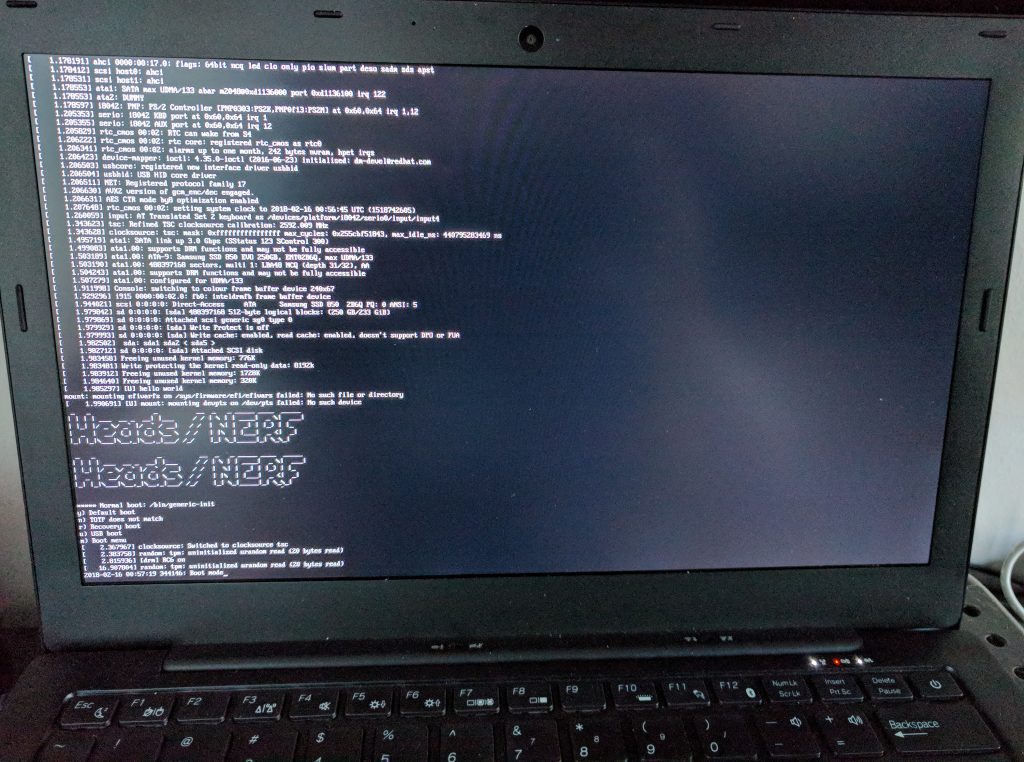
And newer Librems have TPMs bulit-in now.
https://puri.sm/posts/librem-now-most-secure-laptop-under-full-user-with-tamper-evident-features/
Aurora: Providing Trusted System Services for Enclaves On an Untrusted System
Hongliang Liang, Mingyu Li, Qiong Zhang, Yue Yu, Lin Jiang, Yixiu Chen
(Submitted on 10 Feb 2018)
Intel SGX provisions shielded executions for security-sensitive computation, but lacks support for trusted system services (TSS), such as clock, network and filesystem. This makes \textit{enclaves} vulnerable to Iago attacks~\cite{DBLP:conf/asplos/CheckowayS13} in the face of a powerful malicious system. To mitigate this problem, we present Aurora, a novel architecture that provides TSSes via a secure channel between enclaves and devices on top of an untrusted system, and implement two types of TSSes, i.e. clock and end-to-end network. We evaluate our solution by porting SQLite and OpenSSL into Aurora, experimental results show that SQLite benefits from a \textit{microsecond} accuracy trusted clock and OpenSSL gains end-to-end secure network with about 1ms overhead.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Discover the Desktop
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
News from coreboot world
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Just another WordPress.com site
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
You must be logged in to post a comment.