This note explains how to switch a legacy boot Debian/Ubuntu system into a UEFI boot system. Typical use cases: 1) switch a legacy boot installation into an UEFI one, 2) reinstall a broken UEFI boot loader on Debian 7, Debian 8 or Debian 9.[…]
Tag: Debian
Debian 10 released, with Secure Boot
[…]The UEFI (“Unified Extensible Firmware Interface”) support first introduced in Debian 7 (code name “wheezy”) continues to be greatly improved in Debian 10 “buster”. Secure Boot support is included in this release for amd64, i386 and arm64 architectures and should work out of the box on most Secure Boot-enabled machines. This means users should no longer need to disable Secure Boot support in the firmware configuration.[…]
https://lists.debian.org/msgid-search/bcd827ac-a3cf-6695-9a21-9b9d148aed76@debian.org
Hmm, above URL generates an error on the resulting Debian.org-hosted page, but the MARC and Mail-Archive links work, the latter rendered better. The Debian page also wrongly points to the now-dead GMane site, two Debian bugs that need to get fixed…
Debian Secure Boot document updated
Steve McIntyre has updated the Debian wiki page for Secure Boot “to cover a lot more user-facing stuff.”
Debian UEFI Secure Boot changes!
Steve McIntyre has posted an update on Debian’s UEFI Secure Boot status, to the debian-boot and debian-efi mailing lists. Excerpt:
I’ve just pushed changes to a few bits of d-i this weekend to make SB work for amd64:
* build/util/efi-image: […]
* build/config/arm.cfg, build/config/x86.cfg: […]
* debian/control: […]
* grub-installer/grub-installer: […]
The effect of these changes is that the next daily and weekly debian installer images (tomorrow) should Just Work (TM) end-to-end with UEFI Secure Boot. The changes to efi-image also mean that our next live image builds will do SB (for live and installation).
I’ll test all these again in the next couple of days to verify that things have pulled through as I expect, then it’s time to post to d-d-a and write a blog too. We’ve made great progress already. These last changes just tie it all together for end users.
More info:
https://lists.debian.org/msgid-search/20190113192343.qg3ekmtnyepscwxb@tack.einval.com
Debian: call for testing: Secure Boot
Debian UEFI Secure Boot report from DebConf
DebConf, the Debian conference is happening, and there’s a EFI Secure Boot talk. Slides are listed on the debian-efi list below:
https://lists.debian.org/debian-efi/2018/07/msg00015.html
https://meetings-archive.debian.net/pub/debian-meetings/2018/DebConf18/?
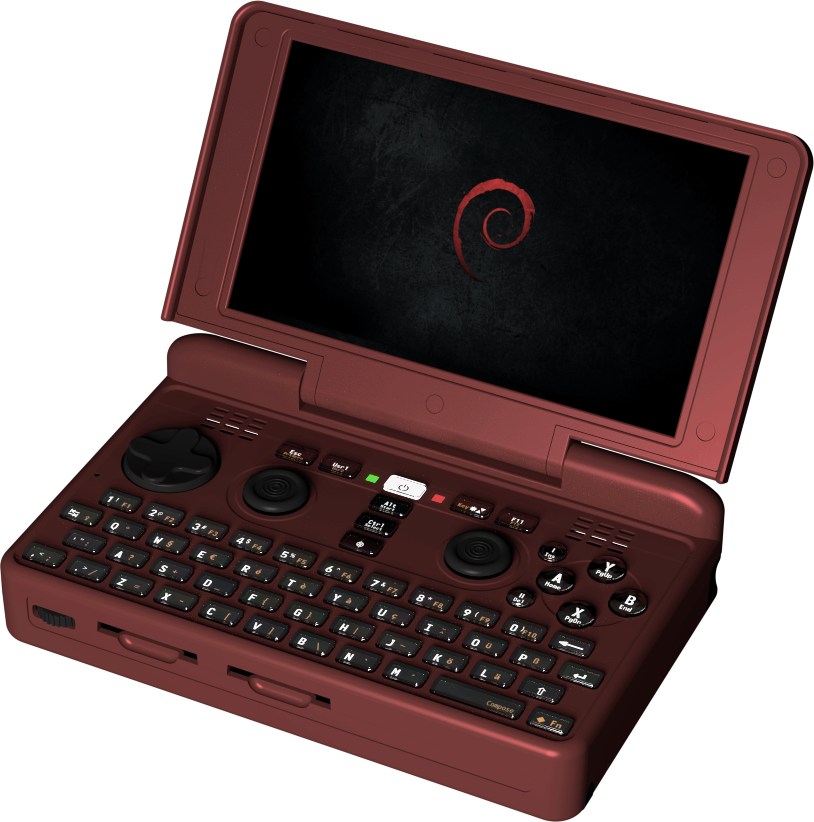
Pyra (Debian-based gaming console) needs kernel ARM/OMAP experts
Pyra needs help by kernel and low-level ARM/OMAP experts
W. Martin Borgert posted a message to the Debian kernel/ARM lists, about soliciting kernel dev help for a Debian-based gaming console, successor to OpenPandora.
Borgert quote:
I just read this post by Pyra project leader Michael Mrozek a.k.a. “Evil Dragon”. (Pyra is planned to be a Debian based gaming console, successor of OpenPandora.) They need help by kernel devs and folks who know OMAP etc. Maybe somebody here can help them? There even might be some money in it. No doubt about fame and fun, though!
Evil Dragon quote:
[…]This brings up another important point: Kernel developers! There’s still quite a few things which should be done before the release. We don’t have proper powersaving, the TILER implementation needs to be tidied up, 3D is not yet implemented, Audio needs a better setup, etc. It seems there are less and less kernel developers having the time to work on such things in their spare time. That’s why I decided to hire freelancers to help out as well![…]I know we’ve got quite a lot of OpenSource fans around here. Maybe some know some good kernel developers, who are able to include and improve hardware support and fix various issues. We can provide a test unit as well as the needed datasheets – but it needs someone who is capable of debugging and fixing low-level things.[…]
https://pyra-handheld.com/boards/threads/moving-along.82982/
https://pyra-handheld.com/
Debian Linux UEFI Secure Boot sprint report
seL ported to RISC-V
seL, in addition to Intel and ARM, now supports RISC-V!
https://github.com/seL4/seL4/tree/master/include/arch/riscv/arch
https://sel4.systems/pipermail/devel/2018-April/001928.html
https://docs.sel4.systems/Hardware/RISCV
https://sel4.systems/About/seL4/
https://riscv.org/
PS: seL is not the only OS porting to RISC-V, here’s the Debian port:
https://groups.google.com/a/groups.riscv.org/forum/#!topic/sw-dev/u4VcUtB9r94
PS: RISC-V is getting active, and has had lots of newsworthy events that I’ve not covered:
https://riscv.org/news/
Debian and FWTS
Re: https://firmwaresecurity.com/2017/11/28/fwts-added-to-debian/
It looks like Canonical’s FWTS is having a hard time staying in Debian repos. 😦
https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=748783
Embedded Linux Japan Technical Jamboree 63 slides/videos uploaded
Status of Embedded Linux, Tim Bird
Review of ELC Europe 2017, Tim Bird
mplementing state-of-the-art U-Boot port, 2017 edition, by Marek Vasut
Linux カーネルのメモリ管理の闇をめぐる戦い(協力者募集中, Tetsuo Handa (NTT Data)
Request for your suggestions: How to Protect Data in eMMC on Embedded Devices, Gou Nakatsuka (Daikin)
Fuego Status and Roadmap, Tim Bird
Multicast Video-Streaming on Embedded Linux environment, Daichi Fukui (TOSHIBA)
From 1 to many Implementing SMP on OpenRISC, Stafford Horne
Core Partitioning Technique on Multicore Linux systems, Kouta Okamoto (TOSHIBA)
Debian + YoctoProject Based Projects: Collaboration Status, Kazuhiro Hayashi (TOSHIBA)
https://elinux.org/Japan_Technical_Jamboree_63#Agenda
See-also: Septemer 2017 Jamboree 62:
Status of Embedded Linux, Tim Bird
EdgeX Foundry: Introduction and demonstration of end to end IoT system, Victor Duan, Linaro
Lighting Talk: Integration between GitLab and Fuego, Tomohito Esaki, IGEL Co., Ltd.
DebConf17 Report, Kazuhiro Hayashi, TOSHIBA
Lightning Talk : About the LTS now, Shinsuke kato, Panasonic Corporation
Kernel Recipes 2015 – Linux Stable Release process, Greg KH
Lightning Talk: IPv6 Ready Logo Test for LTSI 4.9 and introduction about CVE-2016-5863 and CVE-2017-11164, Fan Xin, Fujitsu Computer Technologies Limited
Debsources: browse/search sources of all Debian releases
Matthieu Caneill of Debian announced Debsources. Excerpt of announcement below, for full announcement, see the debian-devel-announce mailing list archives.
https://twitter.com/zacchiro/status/938327579135807488
Announcing sources.debian.org
We’re happy to announce that Debsources, the Web application that allows to browse and search the entire source code of all Debian releases, is now hosted on the official Debian infrastructure and available at https://sources.debian.org . You may already know this service as previously hosted at sources.debian.net . We took the move to Debian hardware as the opportunity to officially announce it here.[…]
https://sources.debian.org
https://codesearch.debian.net/search?q=firmware
https://codesearch.debian.net/search?q=UEFI
https://codesearch.debian.net/search?q=coreboot
Hmm, “EFI” does not work as a search string, and there are Linux-centric UEFI commands that only use “EFI”, not “UEFI”…
FWTS added to Debian
Canonical-based FWTS obviously has Ubuntu packaging, but it now has Debian packaging!
https://ftp-master.debian.org/new/fwts_17.11.00-1.html
Looking forward to seeing an entry for Debian — and any other Linux distro which supports UEFI Secure Boot — alongiside the sole entry by Ubuntu here:
http://kernel.ubuntu.com/git/hwe/fwts.git/tree/src/uefi/securebootcert/sbkeydefs.h
PureOS joins Debian derivatives census
PureOS is the Debian-based Linux distribution by Purism for their laptops. Jonas Smedegaard has apparently joined Purism to help with PureOS:
“I am long time Debian developer with a special interest in Pure Blends (a.k.a. friendly assimilation of derivatives into Debian). Since about a month ago I am hired by Purism to help develop PureOS – a Debian derivative for which I will act as Derivatives Census contact.”
https://wiki.debian.org/Derivatives/Census/PureOS
Hector Oron of Debian, who invited PureOS into the Debian Derivative census, made a few interesting initial comments evaluating PureOS, some things that need I hope Purism addresses:
“The page says that PureOS modifies Debian binary packages. It is quite rare that distributions modify Debian binary packages instead of modifying source packages and rebuilding them. Does PureOS actually do this? If so could you describe what kind of modifications you are making? If not I guess the page needs to be fixed. The apt repository for PureOS does not contain source packages [for the contrib and non-free section], including for packages licensed under the GNU GPL. This may or may not be a copyright violation depending on whether or not you distribute those elsewhere. In any case, please add source packages to your repository so that Debian can automatically create patches to be presented to Debian package maintainers.”
For more info, read the thread on the debian-derivatives@lists.debian.org mailing list.
Hardened Linux: coreboot and CHIPSEC
A bit more information on Hardened Linux’s use of CHIPSEC, in this case coreboot-centric:
“# Enabling some security features at runtime in case of which vendor provided implementation improperly.”
There aren’t many CHIPSEC-based codebases, Hardened Linux is one relatively new one.
Debian 9 “Stretch” released
Excerpts of announcement included below. For full announcement, see the debian-announce mailing list archives.
After 26 months of development the Debian project is proud to present its new stable version 9 (code name “Stretch”), which will be supported for the next 5 years thanks to the combined work of the Debian Security team and of the Debian Long Term Support team. Debian 9 is dedicated to the project’s founder Ian Murdock, who passed away on 28 December 2015.
The UEFI (“Unified Extensible Firmware Interface”) support first introduced in “Wheezy” continues to be greatly improved in “Stretch”, and also supports installing on 32-bit UEFI firmware with a 64-bit kernel. The Debian live images now include support for UEFI booting as a new feature, too.
A total of ten architectures are supported: 64-bit PC / Intel EM64T / x86-64 (amd64), 32-bit PC / Intel IA-32 (i386), 64-bit little-endian Motorola/IBM PowerPC (ppc64el), 64-bit IBM S/390 (s390x), for ARM, armel and armhf for older and more recent 32-bit hardware, plus arm64 for the 64-bit “AArch64” architecture, and for MIPS, in addition to the two 32-bit mips (big-endian) and mipsel (little-endian), there is a new mips64el architecture for 64-bit little-endian hardware. Support for 32- bit Motorola/IBM PowerPC (powerpc) has been removed in “Stretch”.
https://www.debian.org/News/2017/20170617
http://ftp.debian.org/debian/doc/dedication/dedication-9.0.txt
https://www.debian.org/releases/stretch/installmanual
https://www.debian.org/releases/stretch/releasenotes
Debian project seeking OEM partners
https://twitter.com/LucaFilipozzi/status/855830951892353024
OEMs: the Debian project is asking for your help.
Secure Boot BOF at DebConf17
Helen Koike of Collabora has proposed a BOF on UEFI Secure Boot at DebConf17, this August:
DebConf17 – BoF proposal to discuss secure boot
I want to send a BoF proposal to DebConf17 so we can meet there and discuss about secure boot. I would like to know if you are interested in attending and also which topics you suggest for discussion. I would appreciate if you could put your name and suggestions in this form in case you are interested https://goo.gl/forms/lHoEibY1H6FmSHSJ2 , or just reply to this email thread.
For full message, see the debian-efi mailing list archives.
https://lists.debian.org/debian-efi/2017/05/threads.html
https://debconf17.debconf.org/
Debian Live images now include UEFI support
Steve McIntyre gave an update on Debian official images to the debian-(cd, devel-announce,live,cloud) mailing lists. There’s a UEFI update on Debian Live images:
Live images – now including UEFI support
After a hiatus, weekly builds of live images for testing are now happening again. These cover amd64 and i386, and there is a separate image for each of the common desktop environments. Thanks to great work by Neil Williams, Iain Learmonth and Ana Custura on new tools (vmdebootstrap and live-wraper), these also include support for UEFI booting as a new feature. Please help test the images and give feedback:
http://get.debian.org/cdimage/weekly-live-builds/
See Steve’s message to the above-listed lists for the full post.
https://lists.debian.org/msgid-search/20170428012707.GJ28360@einval.com
Debian 9 defers UEFI Secure Boot support
From the latest “Bits from the Release Team” message, it appears that Debian 9 will probably defer Secure Boot support to later.
Secure Boot
At a recent team meeting, we decided that support for Secure Boot in the forthcoming Debian 9 “stretch” would no longer be a blocker to release. The likely, although not certain outcome is that stretch will not have Secure Boot support. We appreciate that this will be a disappointment to many users and developers. However, we need to balance that with the limited time available for the volunteer teams working on this feature, and the risk of bugs being introduced through rushed development. It’s possible that Secure Boot support could be introduced at some point in stretch’s lifetime.
Full message:
https://lists.debian.org/debian-devel-announce/2017/04/msg00013.html
https://wiki.debian.org/SecureBoot
https://wiki.debian.org/UEFI

You must be logged in to post a comment.