During the Spring 2018 UEFI Forum Plugfest, Brent Holtsclaw and John Loucaides of Intel presented an “Introduction to Platform Security.“(slides pdf). There is also a Youtube video: https://www.youtube.com/watch?v=M5krZGV1BLk
I suggest this is required material for anyone interested in this topic!
Slide #8 “Classes of Attacker” with an illustration of attacker power relative to level of access: physical but limited, unlimited physical, and privileged versus unprivileged malware. It is elegant and simple.
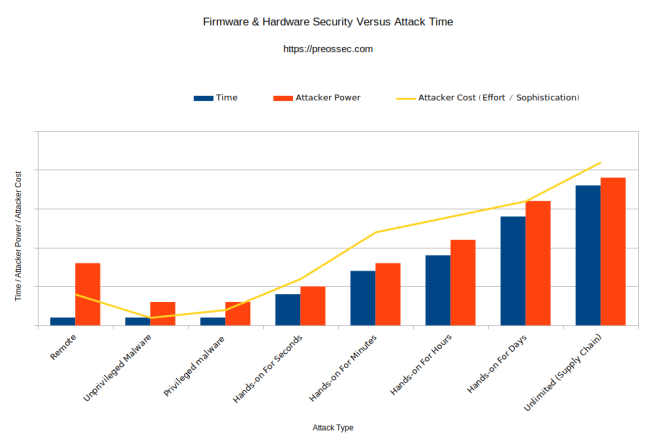
Here’s my chart, inspired by the above, which is neither. Feedback welcome!
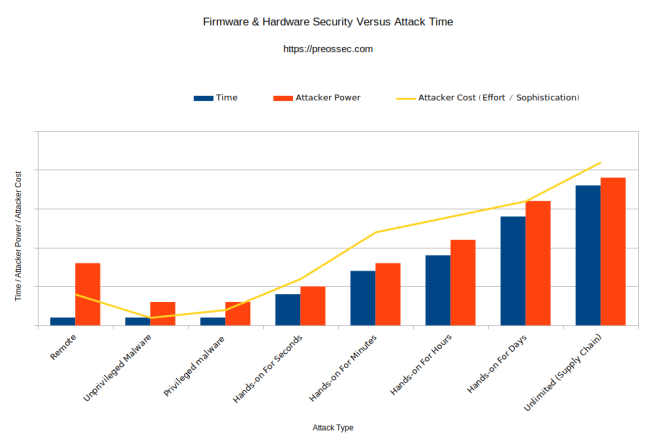
This illustrates graphically what many people have been saying in words. I’ll need to explain it in words anyway. Perfect for a talk! Or a long blog post.
- Scale is:
- fairly precise for time
- fairly precise for attacker power, not quantified in this illustration
- only relative for attacker cost / effort / sophistication
- Attacker power and time are illustrated as bars, to show the discrete nature of each type of attack.
- Time: An attacker who believes they are going to have hands on your hardware for seconds cannot safely assume that they might have minutes or hours.
- Power: An attacker who has the ability to reboot the machine via BMC compromise does not necessarily have the ability to read/write data from the hard drive, as in SATA controller firmware compromise.
- OBSERVATION: Time, attacker power and cost are not always directly correlated. The most dramatic example is remote. By design, remote management systems give the fullest control of their host computer possible, and are full Internet connected computers running an operating system in their own right. A classic “weakest link” – if your BMC is not equally secure to the primary system, then it defines the security of the entire system. Attacking these remotely is just as cheap and efficient as attacking the host system remotely.
- Remote, unprivileged malware and privileged malware share similarity in that:
- they should only be able to compromise unsecured or misconfigured firmware. Unfortunately that is most of the firmware, most of the time.
- ideally they should be verifiable and repairable with software only.
Detail for each type of hardware/firmware attack, as a sort of taxonomy:
Remote
Attacks a management computer built into, or added on to the primary computer. Examples include: IPMI, Redfish, BMCs, Intel AMT and AMD PSP, HP iLo, Dell DRAC, etc. In every way possible, this is the same as simply attacking any network-attached computer. A baseline assumption by manufacturers is often that these specially privileged computers will be attacked to a specially secured network.
Unprivileged Malware
Any standard computer virus / malware can modify at least some of the system firmware, by executing as an unprivileged executable. Special skill and effort is typically required to do this over the creation of a normal virus intended to interact with eg: data files on the filesystem, owned by the unprivileged user. And it is significantly less portable as it often must target a specific SuperIO chip or particular make/model/revision of SATA disk.
Privileged malware
Escalating privilege is understood to be fairly easy on most systems.The primary gain with this attack is using firmware update mechanisms for firmware that can be updated through software (as opposed to requiring direct interaction with the chip in a programmer). UEFI provides the framework for requiring:
- Updates cryptographically signed by the manufacturer
- Forward-only updates, to ensure an attacker cannot revert to an earlier, vulnerable firmware version
But this is not uniformly, or well implemented in the UEFI space, and is not present for most other types of platform firmware.
Hands-on For Seconds
Creates the opportunity for a known-fast side-channel attack, such as the CIA’s “Sonic Screwdriver” exploiting PCIe/Thunderbolt DMA. Or for a stealthy hardware implant, such as the NSA’s Firewalk ethernet jack shim, or an ATM skimmer. Example: Airport security (TSA in the USA) handles a laptop passing through security.
Hands-on For Minutes
Expands the opportunity to slower side-channel attacks, and much more stealthy implants. There may be sufficient time to open the case, and implant something internally, though definitely not for soldering. There is probably an (unillustrated) distinction between hands-on out of sight of the hardware owner, versus in-sight. Example: Airport security (TSA in USA) selects an individual for “enhanced” screening, and separates them from their laptop for some minutes.
Hands-on For Hours
The classic Evil Maid attack, for hardware left unattended in an assumed-safe location such as a hotel room, at home, or an office, or separated from the owner such as at border control for a “suspicious person.” Hours ensures that any case can be opened, and (de)soldering can happen, with the limitation of portable tools only.
Hands-on For Days
An interdiction attack, such as the NSA TAO implants on Cisco routers. More expense and secrecy risk is incurred due to the facilities and number of people involved, but much finer grained (de)soldering is possible.
Unlimited Time (Supply Chain)
Fully invisible implants sandwiched between layers of circuit board are now possible.

But with this revelation, if you have an affected SSD, and you are running Windows, then losing such a laptop may now be a reportable event.