Secure and Efficient RNS software implementation for Elliptic Curve Cryptography
Practical Power Analysis on KCipher-2 Software on Low-End Microcontrollers
Use of simulators for side-channel analysis
Secure positioning: From GPS to IoT
Permutation-based cryptography for embedded and mobile systems
The Curious Case of the Curious Case: Detecting touchscreen events using a smartphone case
Are You Really My Friend? Efficient and Secure Friend-matching in Mobile Social Networks
From Smashed Screens to Smashed Stacks: Attacking Mobile Phones using Malicious Aftermarket Parts
Category: Uncategorized
CHIPSEC whitelist gets updated
FiE
I just noticed FIE, from Usenix Security 2013!
FIE on Firmware: Finding Vulnerabilities in Embedded Systems Using Symbolic Execution
Drew Davidson, Benjamin Moench, Somesh Jha, Thomas Ristenpart
Embedded systems increasingly use software-driven low-power microprocessors for security-critical settings, surfacing a need for tools that can audit the security of the software (often called firmware) running on such devices. Despite the fact that firmware programs are often written in C, existing source-code analysis tools do not work well for this setting because of the specific architectural features of low-power platforms. We therefore design and implement a new tool, called FIE, that builds off the KLEE symbolic execution engine in order to provide an extensible platform for detecting bugs in firmware programs for the popular MSP430 family of microcontrollers. FIE incorporates new techniques for symbolic execution that enable it to verify security properties of the simple firmwares often found in practice. We demonstrate FIE’s utility by applying it to a corpus of 99 open-source firmware programs that altogether use 13 different models of the MSP430. We are able to verify memory safety for the majority of programs in this corpus and elsewhere discover 21 bugs.
http://pages.cs.wisc.edu/~davidson/fie/
pages.cs.wisc.edu/~davidson/fie/fie.tgz
http://pages.cs.wisc.edu/~davidson/fie/directions.html
https://www.usenix.org/conference/usenixsecurity13/technical-sessions/paper/davidson
FDA Workshop: Cybersecurity of Medical Devices
https://twitter.com/scotterven/status/856594905812000768
[…]Cybersecurity of medical devices was identified as one of the top ten regulatory science gaps. […]The scope and nature of this cybersecurity regulatory science research framework is designed to be broad to foster collaboration across all interested stakeholders. The domain is defined by the intersection of safety and security in the design and evolution of medical devices. The objective of the workshop is to facilitate a discussion on the current state of regulatory science in the field of cybersecurity of medical devices, with a focus on patient safety.[…]
https://www.fda.gov/MedicalDevices/NewsEvents/WorkshopsConferences/ucm549732.htm
PCIleech progress continues…
Manticore
Manticore is a prototyping tool for dynamic binary analysis, with support for symbolic execution, taint analysis, and binary instrumentation.
Features
* Input Generation: Manticore automatically generates inputs that trigger unique code paths
* Crash Discovery: Manticore discovers inputs that crash programs via memory safety violations
* Execution Tracing: Manticore records an instruction-level trace of execution for each generated input
* Programmatic Interface: Manticore exposes programmatic access to its analysis engine via a Python API
Rescatux adds new UEFI rescue options
Adrian announced Rescatux 0.41b, with new UEFI rescue options:
(*) Change UEFI Boot order
(*) Create UEFI Boot Entry
(*) Fake Microsoft Windows UEFI.
(*) Hide Microsoft Windows UEFI
(*) Reinstall Microsoft Windows UEFI boot entries
Adrian has a thread on the debian-efi list, asking for feedback on these features. Excerpt of announcement below, see the full announcement on the debian-efi list.
Rescatux 0.41b1 released with UEFI rescue options
* Rescatux introduction
Rescatux is a GNU/Linux rescue cd (and eventually also Windows) but it is not like other rescue disks. Rescatux comes with Rescapp. Rescapp is a nice wizard that will guide you through your rescue tasks.[…]
* Rescatux 0.41b1 released
Last week I released Rescatux 0.41b1 with a bunch of new UEFI rescue options. I just wanted to share with you some technical details about those options so that I can get some feedback from you.[…]
http://wiki.rescatux.org/wiki/Main_Page
ALT Linux Rescue also has the option to boot either into their Linux or into their provided UEFI Shell. I wish more Linux distirbutions provided features like this.
ARM Releases Machine Readable Architecture Specification
TaLoS: library that integrates Intel SGX with OpenSSL
TaLoS: Efficient TLS Termination Inside SGX Enclaves for Existing Applications
TaLoS1 is a TLS library that allows existing applications (with an OpenSSL/LibreSSL interface) to securely terminate their TLS connection. For this, TaLoS places security-sensistive code and data of the TLS library inside an Intel SGX enclave, while the rest of the application remains outside. It can then be used as the building block for a wide range of security-critical applications for which the integrity and/or confidentiality of TLS connections must be guaranteed. TaLoS provides good performance by executing enclave transitions asynchronously and leveraging user-level threading inside the enclave. The code is accompanied with a technical report, containing details about the architecture and performance results. In contrast to the SSL add-on for the Intel SGX SDK, TaLoS exposes the OpenSSL/LibreSSL API to untrusted code outside of the enclave. This means that existing applications can use the TaLoS library with no or only minor modifications. The Intel SGX SDK SSL add-on does not expose an outside interface, which means that applications must be modified to use it.[…]
ShowPCIx: UEFI tool to show PCI devices using PCI.IDS database
HardwareX: first issue published
https://twitter.com/jodangeeto/status/854315266729234433
HardwareX is an open access journal established to promote free and open source designing, building and customizing of scientific infrastructure (hardware). HardwareX aims to recognize researchers for the time and effort in developing scientific infrastructure while providing end-users with sufficient information to replicate and validate the advances presented. HardwareX is open to input from all scientific, technological and medical disciplines. Scientific infrastructure will be interpreted in the broadest sense. Including hardware modifications to existing infrastructure, sensors and tools that perform measurements and other functions outside of the traditional lab setting (such as wearables, air/water quality sensors, and low cost alternatives to existing tools), and the creation wholly new tools for either standard or novel laboratory tasks. Authors are encouraged to submit hardware developments that address all aspects of science, not only the final measurement, for example, enhancements in sample preparation and handling, user safety, and quality control. The use of distributed digital manufacturing strategies (e.g. 3-D printing) are encouraged. All designs must be submitted under an open hardware license.
An efficient and cost effective FPGA based implementation of the Viola-Jones face detection algorithm
Peter Irgens | Curtis Bader | Theresa Lé | Devansh Saxena | Cristinel Ababei
An open source automatic feeder for animal experiments
Jinook Oh | Riccardo Hofer | W. Tecumseh Fitch
Open source laboratory sample rotator mixer and shaker
Karankumar C. Dhankani | Joshua M. Pearce
A high performance, low power computational platform for complex sensing operations in smart cities
Jiming Jiang | Christian Claudel
A plug’n’play WiFi surface-mount dual-loop antenna
Pedro Chamorro-Posada | José Vázquez-Cabo | José L. Rodríguez | José M. López-Santos
A time-sorting pitfall trap and temperature datalogger for the sampling of surface-active arthropods
Marshall S. McMunn
Open source IoT meter devices for smart and energy-efficient school buildings
Lidia Pocero | Dimitrios Amaxilatis | Georgios Mylonas | Ioannis Chatzigiannakis
https://www.journals.elsevier.com/hardwarex/#openscience
https://www.journals.elsevier.com/hardwarex/recent-articles
Unicorn Emulator 1.0.1 released
Nguyen Anh Quynh announced the 1.0.1 release of the Unicorn CPU Emulator.
[unicorn-engine] Unicorn Emulator v1.0.1 is out!
We are excited to announce version 1.0.1 for Unicorn CPU Emulator framework! This is a stable release, in which we fixed some issues in the core, added some features on Arm, Arm64, Mips & X86. […]
https://www.freelists.org/post/unicorn-engine/Unicorn-Emulator-v101-is-out
http://www.unicorn-engine.org/Version-1.0.1
https://github.com/unicorn-engine/unicorn/releases/tag/1.0.1
http://www.keystone-engine.org
http://www.capstone-engine.org
http://www.unicorn-engine.org
Attacking ARM TrustZone using RowHammer
CHIPSEC_GUI
There’s a relatively new GUI front-end to the command line-based CHIPSEC project, called CHISPEC_GUI. This GUI for chipsec 1.2.5 provides a fairly simple design but lets you select each module that you want to run. It is made with PyQt4. It is getting updated to Chipsec 1.3.0 with the appropriate module additions written into the GUI. It was originally written in Persian by Emad Helmi, and translated to English by Alex Floyd of PreOS-Security.
English version:
https://www.github.com/mex20/chipsec_gui
Forked from Persian version:
https://www.github.com/EmadHelmi/chipsec_gui
Microsoft seeks U-Boot Linux firmware Engineer
Senior Software Engineer, Linux Firmware – CSI / Azure – Cloud Server Infrastructure
The Cloud Server Infrastructure Firmware Development (CSI-FW) team is responsible for server hardware definition, design and development of Server and Rack Infrastructure engineering for Microsoft’s online services. […] This role will be for a highly-motivated Firmware Engineer with a solid background in embedded system design using embedded Linux. […] Required Qualifications:
[…]
* Extensive knowledge of u-boot customization, Linux kernel internals and adding new hardware drivers
[…]
https://careers.microsoft.com/jobdetails.aspx?jid=282596
microparse
“Microparse: Microcode update parser for AMD, Intel, and VIA processors written in Python 3.x.”
Security Analysis of x86 Processor Microcode
Daming D. Chen, Gail-Joon Ahn
December 11, 2014
Modern computer processors contain an embedded firmware known as microcode that controls decode and execution of x86 instructions. Despite being proprietary and relatively obscure, this microcode can be updated using binaries released by hardware manufacturers to correct processor logic faws (errata). In this paper, we show that a malicious microcode update can potentially implement a new malicious instructions or alter the functionality of existing instructions, including processor-accelerated virtualization or cryptographic primitives. Not only is this attack vector capable of subverting all software-enforced security policies and access controls, but it also leaves behind no postmortem forensic evidence due to the volatile nature of write-only patch memory embedded within the processor. Although supervisor privileges (ring zero) are required to update processor microcode, this attack cannot be easily mitigated due to the implementation of microcode update functionality within processor silicon. Additionally, we reveal the microarchitecture and mechanism of microcode updates, present a security analysis of this attack vector, and provide some mitigation suggestions. A tool for parsing microcode updates has been made open source, in conjunction with a listing of our dataset.
https://github.com/ddcc/microparse
Click to access 2014_paper_microcode.pdf
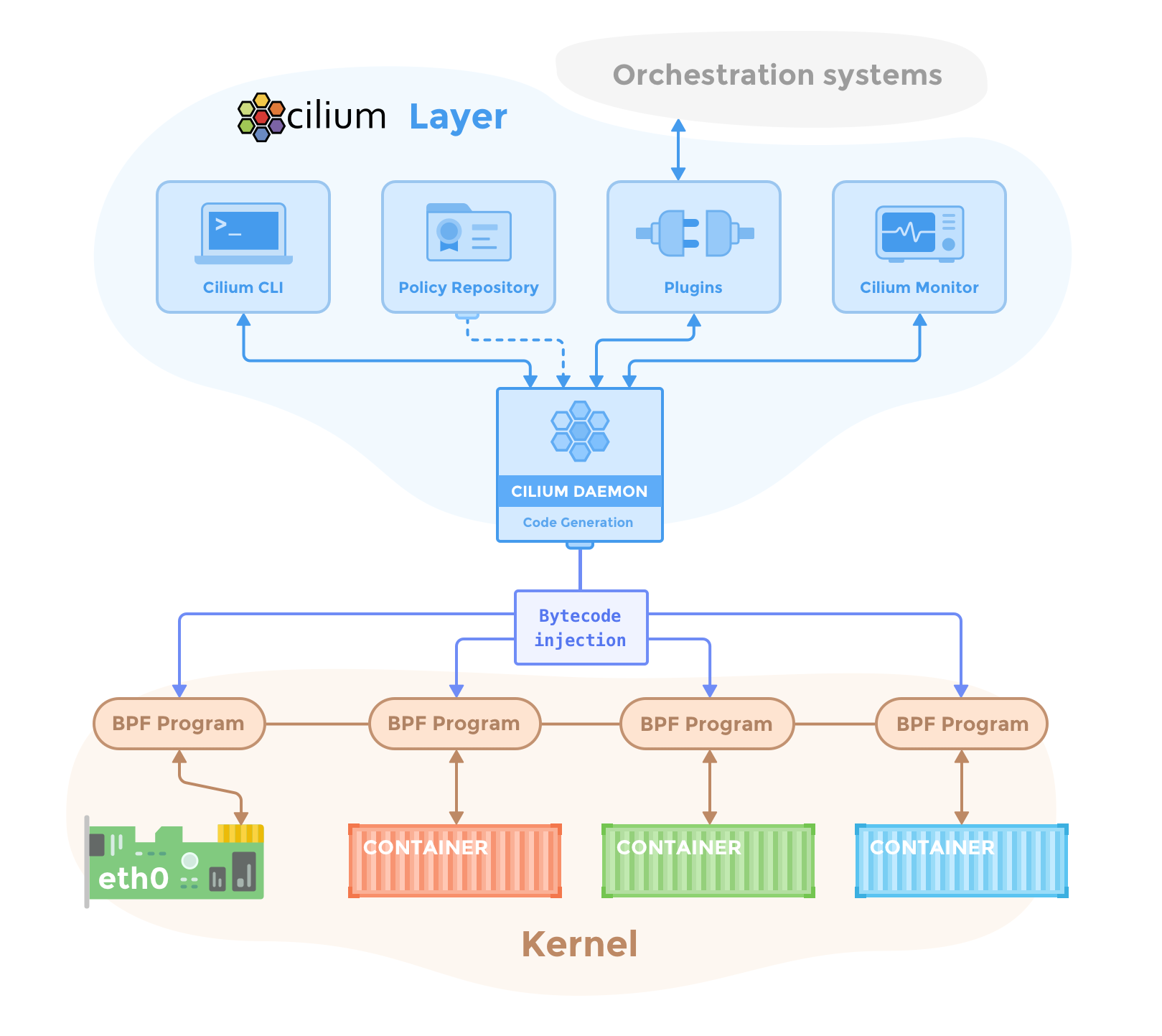
Docker: LinuxKit (and Cilium)
IBM updates Linux IMA to improve boot security
Thiago Jung Bauermann of IBM has submitted a 6-part patch to the Linux-IMA-devel/Linux-Kernel lists, with some improvements to Linux IMA for OpenPOWER secure/trusted boot. Including comments from parts 1 and 6 of the patch, see the full patch for full details.
Appended signatures support for IMA appraisal
On the OpenPOWER platform, secure boot and trusted boot are being implemented using IMA for taking measurements and verifying signatures. Since the kernel image on Power servers is an ELF binary, kernels are signed using the scripts/sign-file tool and thus use the same signature format as signed kernel modules. This patch series adds support in IMA for verifying those signatures. It adds flexibility to OpenPOWER secure boot, because it can boot kernels with the signature appended to them as well as kernels where the signature is stored in the IMA extended attribute. The first four patches are cleanups and improvements that can be taken independently from the others (and from each other as well). The last two are the ones actually focused on this feature. […] This patch introduces the appended_imasig keyword to the IMA policy syntax to specify that a given hook should expect the file to have the IMA signature appended to it. Here is how it can be used in a rule:
appraise func=KEXEC_KERNEL_CHECK appraise_type=appended_imasig
appraise func=KEXEC_KERNEL_CHECK appraise_type=appended_imasig|imasig
In the second form, IMA will accept either an appended signature or a signature stored in the extended attribute. In that case, it will first check whether there is an appended signature, and if not it will read it from the extended attribute. The format of the appended signature is the same used for signed kernel modules. This means that the file can be signed with the scripts/sign-file tool, with a command line such as this:
$ sign-file sha256 privkey_ima.pem x509_ima.der vmlinux
This code only works for files that are hashed from a memory buffer, not for files that are read from disk at the time of hash calculation. In other words, only hooks that use kernel_read_file can support appended signatures. The change in CONFIG_INTEGRITY_SIGNATURE to select CONFIG_KEYS instead of depending on it is to avoid a dependency recursion in CONFIG_IMA_APPRAISE_APPENDED_SIG, because CONFIG_MODULE_SIG_FORMAT selects CONFIG_KEYS and Kconfig complains that CONFIG_INTEGRITY_SIGNATURE depends on it.
https://lists.sourceforge.net/lists/listinfo/linux-ima-devel
Shell script for Laszlo’s SMM test environment article
Laszlo Ersek of Red Hat wrote a wiki article on tianocore.org[1], showing how to setup the EDK2 with QEMU/OVMF for testing SMM code using Fedora.
Recently, Alex Floyd of PreOS Security wrote a shell script to codify this wiki article[2].
Laszlo’s wiki is dense, I expect this script will be useful for some UEFI firmware engineers and security researchers.
According to Alex, “some things needed tweaking to get to work, and the Windows portion of the tutorial is not included in the script.”
[1] https://github.com/tianocore/tianocore.github.io/wiki/Testing-SMM-with-QEMU,-KVM-and-libvirt
[2] https://github.com/gencymex/smmtestbuildscript
https://github.com/gencymex/smmtestbuildscript/blob/master/smmtesthost.sh
Intel cancels Intel Developer Forum
http://www.anandtech.com/show/11279/intel-discontinues-the-intel-developer-forum-idf17-cancelled
PS: In other event news, the Fall UEFI Plugfest will be in Taipei instead of Seattle. See the presentations from the last plugfest for details.

You must be logged in to post a comment.