flare-emu marries IDA Pro’s binary analysis capabilities with Unicorn’s emulation framework to provide the user with an easy to use and flexible interface for scripting emulation tasks. It is designed to handle all the housekeeping of setting up a flexible and robust emulator for its supported architectures so that you can focus on solving your code analysis problems. Currently, flare-emu supports the x86, x86_64, ARM, and ARM64 architectures.[…]
Tag: Unicorn
EternalRed0’s Unicorn Engine tutorial
Unicorn Engine tutorial
Jan 14, 2018
In this tutorial you will learn how to use Unicorn Engine by solving practical exercises. There are 4 exercises and I will solve the first exercise for you. For the others I am providing hints and solutions, which you can obtain by clicking the spoiler buttons.[…]
http://eternal.red/2018/unicorn-engine-tutorial/
AFL-Unicorn: fuzz any architecture supported by Unicorn
https://twitter.com/revskills/status/928382801400991744
afl-unicorn let’s you fuzz any piece of binary that can be emulated by Unicorn Engine.
https://github.com/njv299/afl-unicorn
http://www.unicorn-engine.org/
https://hackernoon.com/afl-unicorn-fuzzing-arbitrary-binary-code-563ca28936bf
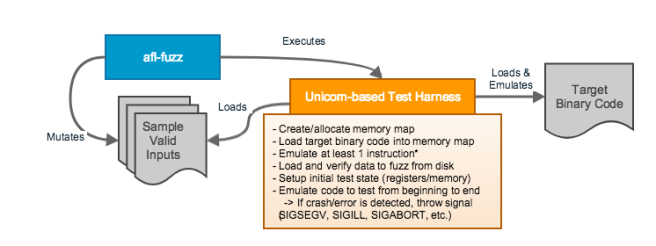
[…]Unicorn Mode works by implementing the block-edge instrumentation that AFL’s QEMU Mode normally does into Unicorn Engine. Basically, AFL will use block coverage information from any emulated code snippet to drive its input generation. The whole idea revolves around proper construction of a Unicorn-based test harness, as shown in the figure below:
uEmu: Unicorn-based emulator plugin for IDA
uEmu is a tiny cute emulator plugin for IDA based on unicorn engine.
Supports following architectures out of the box: x86, x64, ARM, ARM64.
What is it GOOD for?
* Emulate bare metal code (bootloaders, embedded firmware etc)
* Emulate standalone functions
https://github.com/alexhude/uEmu

Unicorn Emulator 1.0.1 released
Nguyen Anh Quynh announced the 1.0.1 release of the Unicorn CPU Emulator.
[unicorn-engine] Unicorn Emulator v1.0.1 is out!
We are excited to announce version 1.0.1 for Unicorn CPU Emulator framework! This is a stable release, in which we fixed some issues in the core, added some features on Arm, Arm64, Mips & X86. […]
https://www.freelists.org/post/unicorn-engine/Unicorn-Emulator-v101-is-out
http://www.unicorn-engine.org/Version-1.0.1
https://github.com/unicorn-engine/unicorn/releases/tag/1.0.1
http://www.keystone-engine.org
http://www.capstone-engine.org
http://www.unicorn-engine.org
Unicorn-based EFI emulator?
OSX Reverser has a new blog post on Apple EFI firmware passwords:
https://twitter.com/osxreverser/status/746479354570477568
[…] This is when I had an idea! How about creating an EFI emulator and debugger using the Unicorn Engine framework? I had a feeling this wouldn’t be extremely hard and time consuming because the EFI environment is self contained – for example no linkers and syscalls to emulate. I also knew that this binary was more or less isolated, only using a few Boot and RunTime services and very few external protocols. Since the total number of Boot and RunTime services are very small this meant that there wasn’t a lot of code to be emulated. And with a couple of days work the EFI DXE Emulator was born. To my surprise I was finally able to run and debug an EFI binary in userland, speeding the reverse engineering process up immensely and quickly providing insight to previously tricky code. […]
https://reverse.put.as/2016/06/25/apple-efi-firmware-passwords-and-the-scbo-myth/
https://sentinelone.com/blogs/apple-efi-firmware-passwords-and-the-scbo-myth/
Looking forward to an URL to this EFISwissKnife IDA plugin, and ESPECIALLY this new Unicorn-based EFI emulator! I can’t find an URL yet, though. 😦
ARMSCGen: ARM Shellcode Generator
ARM Shellcode Generator: Shellcodes for ARM/Thumb mode. Ideas came from shell-storm and pwntools/pwnies. Thanks to share all of brilliant sources on the net. I’m interested in mobile platform and archtecture like Android on ARM, Router on MIPS and so on. This project named ARMSCGen focus on shellcode on ARM Architecture especially ARMv7 Thumb Mode.
ROPMEMU
ROPMEMU is a framework to analyze, dissect and decompile complex code-reuse attacks. It adopts a set of different techniques to analyze ROP chains and reconstruct their equivalent code in a form that can be analyzed by traditional reverse engineering tools. In particular, it is based on memory forensics (as its input is a physical memory dump), code emulation (to faithfully rebuild the original ROP chain), multi-path execution (to extract the ROP chain payload), CFG recovery (to rebuild the original control flow), and a number of compiler transformations (to simplify the final instructions of the ROP chain). Specifically, the memory forensics part is based on Volatility plugins. The emulation and the multi-path part is implemented through the Unicorn emulator. […]
cemu – Cheap EMUlator: Qt GUI of Keystone, Unicode, Capstone
Hugsy has created cemu, the Cheap EMUlator that shellcoders will enjoy:
Cheap EMUlator is a simple tool to combine together all the features of Keystone, Unicorn and Capstone engines in a Qt powered GUI. It allows to test binary samples, check your shellcodes or even simply learn how to write assembly code, all of this for the following architectures:
x86-32 / x86-64
Arm / AArch64
MIPS / MIPS64
SPARC / SPARC64
(more to come)
Pre-Requisites:
unicorn and its Python bindings, as the emulation engine
keystone and its Python bindings, as the assembly engine
capstone and its Python bindings, as the disassembly engine
PyQt5 for the GUI
pygments for the text colorization
Moar info:
https://github.com/hugsy/cemu
Keystone Project announced
Nguyen Anh Quynh announced the Keystone Engine Project, with an IndieGogo funding campaign to help them:
We are very excited to announce our IndieGogo campaign for Keystone Engine, the next-gen assembler framework! After Capstone & Unicorn, Keystone is the latest of our on-going effort to bring better tools to the reverse-engineering community. Now with the final missing piece Keystone, we complete the magical trilogy of disassembler – emulator – assembler. Come support us, and help to spread the news, so together we can solve the lingering problem of missing the assembler framework once, and for all! The Keystone name came from some private conversation with Felix “FX” Lindner. Thanks for such a great inspiration, FX!
http://www.capstone-engine.org
http://www.unicorn-engine.org
http://www.keystone-engine.org
https://igg.me/at/keystone
Unicorn Engine released
https://twitter.com/revskills/status/654722178298986496
Unicorn is a lightweight, multi-platform, multi-architecture CPU emulator framework based on QEMU. Unicorn offers some unparalleled features:
* Multi-architecture: ARM, AMM64 (ARMv8), M68K, MIPS, SPARC, and X86 (16, 32, 64-bit)
* Clean/simple/lightweight/intuitive architecture-neutral API
* Implemented in pure C language, with bindings for Python, Java, and Go
* Native support for Windows & *nix (with Mac OSX, Linux, *BSD & Solaris confirmed)
* High performance via Just-In-Time compilation
* Support for fine-grained instrumentation at various levels
* Thread-safety by design
Unicorn was announced at BlackHat this Summer, and the source for this open source project just got released. Looking forward to using this to debug firmware …but even though it is based on QEMU, I don’t see how to Unicorn to work with OVMF. If someone knows how, please post a Comment with info!
https://github.com/unicorn-engine/unicorn
http://www.unicorn-engine.org/
https://www.blackhat.com/us-15/briefings.html#unicorn-next-generation-cpu-emulator-framework
Click to access us-15-Nguyen-Unicorn-Next-Generation-CPU-Emulator-Framework.pdf
