https://ami.com/en/tech-blog/warning-be-careful-with-free-usb-devices/
Tag: USB
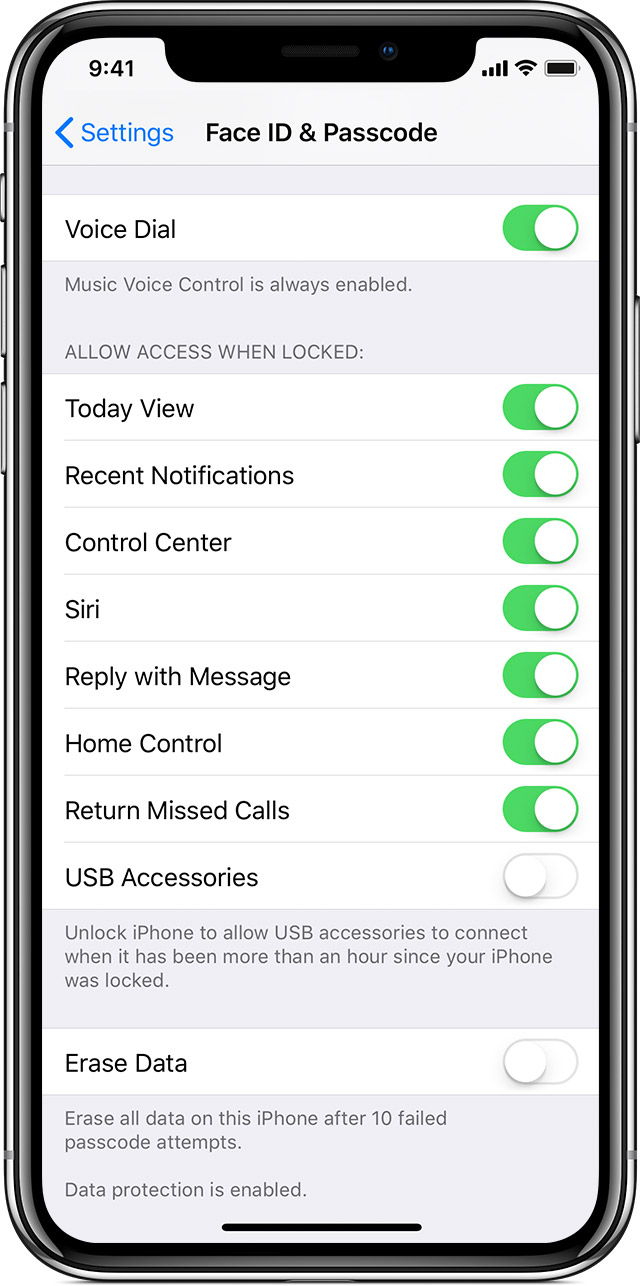
ElcomSoft: USB Restricted Mode inside out
ElcomSoft: This $39 Device Can Defeat iOS USB Restricted Mode
[…]In other words, we have found no obvious way to break USB Restricted Mode once it is already engaged. However, we discovered a workaround, which happens to work exactly as we suggested back in May[…]
https://blog.elcomsoft.com/2018/07/this-9-device-can-defeat-ios-usb-restricted-mode/
Apple: Using USB accessories with iOS 11.4.1 and later
USB Pwny Express – Counterfeit USB Devices and Anti-Forensics
[…]USB Hardware, Counterfeit USB Devices, and Firmware Mayhem[…]
https://www.gillware.com/forensics/blog/articles/counterfeit-usb-devices-antiforensics/
Two more BadUSB-related articles
WiFi HID Injector – An USB Rubberducky / BadUSB On Steroids
WooKey: USB Devices Strike Back
WooKey: USB Devices Strike Back
Date : 13 juin 2018 à 17:15 — 30 min.
The USB bus has been a growing subject of research in recent years. In particular, securing the USB stack (and hence the USB hosts and devices) started to draw interest from the academic community since major exploitable flaws have been revealed by the BadUSB threat. The work presented in this paper takes place in the design initiatives that have emerged to thwart such attacks. While some proposals have focused on the host side by enhancing the Operating System’s USB sub-module robustness, or by adding a proxy between the host and the device, we have chosen to focus our efforts on the device side.
https://www.sstic.org/2018/presentation/wookey_usb_devices_strike_back/
CIRCLean: USB Sanitizer
https://www.circl.lu/projects/CIRCLean/
Malware regularly uses USB sticks to infect victims, and the abuse of USB sticks is a common vector of infection (as an example Lost USB keys have 66% chance of malware). CIRCLean is an independent hardware solution to clean documents from untrusted (obtained) USB keys / USB sticks. The device automatically converts untrusted documents into a readable but disarmed format and stores these clean files on a trusted (user owned) USB key/stick. The focus of CIRCLean is to establish document exchange even if the used transport layer (the USB stick) cannot be trusted or if there is a suspicion about whether the contained documents are free of malware or not. In the worst case, only the CIRCLean would be compromised, but not the computer reading the target (trusted) USB key/stick. The code runs on a Raspberry Pi (a small hardware device), which also means it is not required to plug the original USB key into a computer. CIRCLean can be seen as a kind of air gap between the untrusted USB key and your operational computer. CIRCLean does not require any technical prerequisites of any kind and can be used by anyone. CIRCLean is free software which can be audited and analyzed by third-parties. We also invite all organizations to actively reuse CIRCLean in their own products or contribute to the project.[…]

more on WebUSB and recent YubiCo vuln
Re: https://firmwaresecurity.com/2018/06/14/yubico-vs-security-researchers/
here’s a bit more on WebUSB and recent YubiKey vuln, latter blog post has great background on WebUSB tech.
http://pwnaccelerator.github.io/2018/webusb-yubico-disclosure.html
https://labs.mwrinfosecurity.com/blog/webusb/
https://developers.google.com/web/updates/2016/03/access-usb-devices-on-the-web
From intro paragraph of Google’s intro to WebUSB (emphasis theirs):
“[…]But most importantly this will make USB safer and easier to use by bringing it to the Web.”
LOL
PS: Anyone here a Wikipedia editor? This page needs an entry for WebUSB:
https://en.wikipedia.org/wiki/Category:USB
and perhaps a dedicated page for WebUSB not just:
https://en.wikipedia.org/wiki/Google_Chrome
Besides WebUSB and Wireless USB, what other scary OOB interfaces to USB exist?! I really need to spend more time learning USB properly…
Un-Sexy Headline: USB Restricted Mode Will Improve iPhone User Security
https://twitter.com/Riana_Crypto/status/1007398287622590464
By Riana Pfefferkorn on June 14, 2018 at 4:01 pm
In the upcoming version of the Apple iPhone iOS operating system, iOS 12, the phone’s Lightning cable port (used for charging and data transmission) will be disabled an hour after the phone is locked. The device will still charge, but transferring data to or from the device via the Lightning cable will require entering the device’s password first. Connecting to the data port via Lightning cable is what third-party forensic devices called Cellebrite and GrayKey rely upon to extract data from locked, encrypted iPhones. These tools (made, respectively, by the eponymous Cellebrite and a company called Grayshift) are employed by U.S. law enforcement agencies at federal, state, and local levels. Unsurprisingly, just about everybody covering the story is framing Apple’s move as one that will thwart law enforcement.[…]
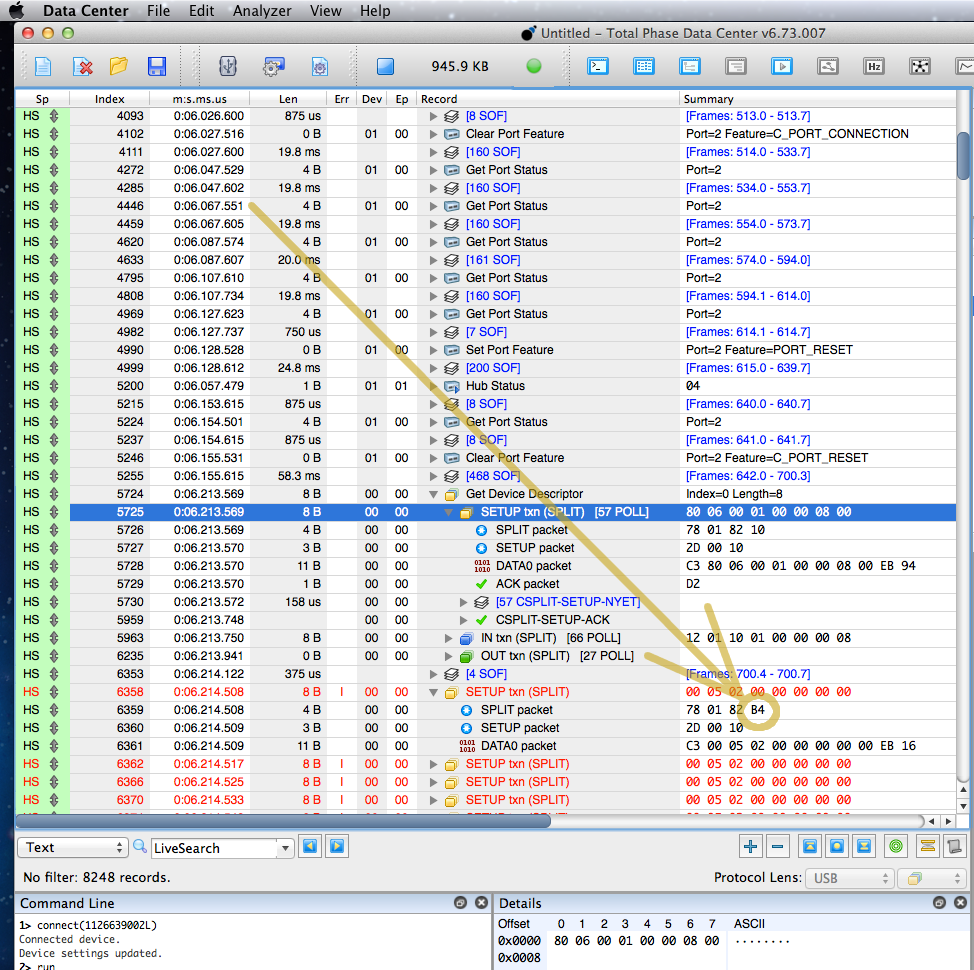
USB Hub Bug Hunting and Lessons Learned
In this article I’ll show how a protocol analyzer is used, how my instincts turned out to be very wrong, and along the way dive into arcane USB details you probably won’t see explained anywhere else.[…]
https://www.pjrc.com/usb-hub-bug-hunting-lessons-learned/
USB Reverse Engineering: A Universal Guide
USB Reverse Engineering: A Universal Guide
by: Ben James
May 25, 2018
[Glenn ‘devalias’ Grant] is a self-proclaimed regular rabbit hole diver and is conscious that, between forays into specific topics, short-term knowledge and state of mind can be lost. This time, whilst exploring reverse engineering USB devices, [Glenn] captured the best resources, information and tools – for his future self as well as others. His guide is impressively comprehensive, and covers all the necessary areas in hardware and software.[…]
The Evil Mouse Project
Conclusion: Never trust USB devices (and not only storage devices…)
https://blog.rootshell.be/2018/05/22/evil-mouse-project/

Spoofing Cell Networks with a USB to VGA Adapter
Bad Ducky: Rubber Ducky compatible clone based on CJMCU BadUSB HW
The below articles point to related tools, besides the Hak5 Rubber Ducky.
https://github.com/mharjac/bad_ducky
https://twitter.com/anonymous9396/status/983165816160972806
https://www.kitploit.com/2018/04/bad-ducky-rubber-ducky-compatible-clone.html
See-also:
https://ducktoolkit.com/viewscript/all/
https://github.com/hak5darren/USB-Rubber-Ducky/wiki/Payloads

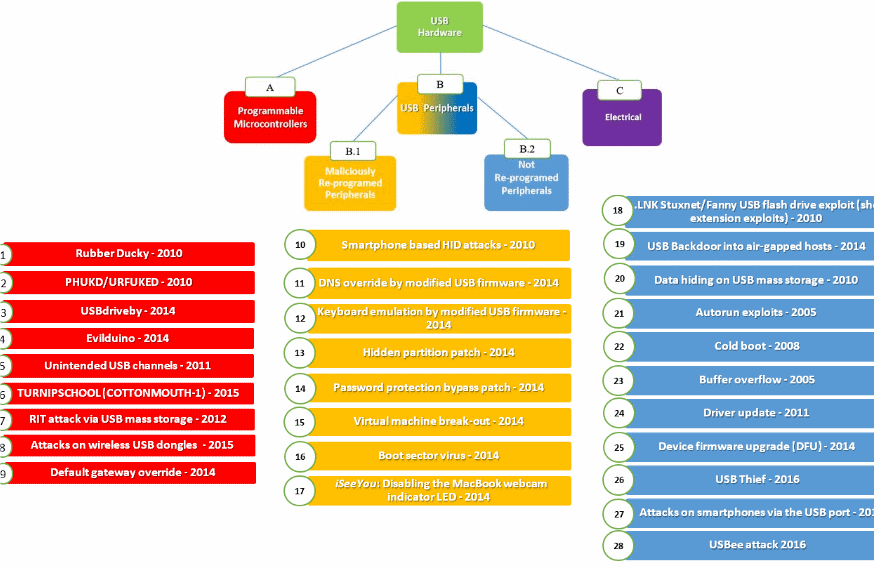
list of 29 USB-based attacks
https://twitter.com/campuscodi/status/973723887891464192
USB-based attacks
Nir Nissim, Ran Yahalom, Yuval Elovici
Attackers increasingly take advantage of innocent users who tend to use USB peripherals casually, assuming these peripherals are benign when in fact they may carry an embedded malicious payload that can be used to launch attacks. In recent years, USB peripherals have become an attractive tool for launching cyber-attacks. In this survey, we review 29 different USB-based attacks and utilize our new taxonomy to classify them into four major categories. These attacks target both individuals and organizations; utilize widely used USB peripherals, such as keyboards, mice, flash drives, smartphones etc. For each attack, we address the objective it achieves and identify the associated and vulnerable USB peripherals and hardware.
https://doi.org/10.1016/j.cose.2017.08.002
https://www.sciencedirect.com/science/article/pii/S0167404817301578
https://www.bleepingcomputer.com/news/security/heres-a-list-of-29-different-types-of-usb-attacks/
UefiUsbScan.efi: Scan USB host controllers and connections, written in FASM
UefiUsbScan: Scan for USB host controllers and connections, current version use direct PCI/MMIO hardware access. Only xHCI controllers supported yet, not supports UHCI, OHCI, EHCI.
X41 D-Sec GmbH browser security whitepaper: WebUSB, WebBluetooth, WebSMM
This white paper provides a technical comparison of the security features and attack surface of Google Chrome, Microsoft Edge, and Internet Explorer. We aim to identify which browser provides the highest level of security in common enterprise usage scenarios, and show how differences in design and implementation of various security technologies in modern web browsers might affect their security. Comparisons are done using a qualitative approach since many issues regarding browser security cannot easily be quantified. We focus on the weaknesses of different mitigations and hardening features and take an attacker’s point of view. This should give the reader an impression about how easy or hard it is to attack a certain browser. The analysis has been sponsored by Google. X41 D-Sec GmbH accepted this sponsorship on the condition that Google would not interfere with our testing methodology or control the content of our paper. We are aware that we could unconsciously be biased to produce results favorable to our sponsor, and have attempted to eliminate this by being as transparent as possible about our decision-making processes and testing methodologies.
Click to access X41-Browser-Security-White-Paper.pdf
https://www.x41-dsec.de/#about
https://www.x41-dsec.de/security/report/whitepaper/2017/09/18/whitepaper-x41-browser-security/
TinyFPGA bootloader moves
https://twitter.com/TinyFPGA/status/958572873043664896
https://github.com/tinyfpga/TinyFPGA-Bootloader
“An open source USB bootloader for FPGAs”



You must be logged in to post a comment.