[…]…This post will describe how I solved simple.gb, a Gameboy ROM challenge written by @condret. It was actually my first time reversing a Gameboy ROM — and it was awesome![…]
Author: hucktech
Intel Whitepaper updated: Using IOMMU for DMA Protection in UEFI Firmware
We recommend firmware developers review this docment to understand threats from unauthorized internal DMA, as well as DMA from non-PCI devices that platform firmware may configure. Using an IOMMU such as Intel VT-d allows fine-grain control of memory protection without broadly disabling bus-mastering capabilities in the pre-boot space.
Note: this whitepaper was originally published under the title “A Tour beyond BIOS Using Intel® VT-d for DMA Protection in UEFI BIOS” in January 2015.
https://firmware.intel.com/blog/updated-whitepaper-using-iommu-dma-protection-uefi-firmware
Click to access Intel_WhitePaper_Using_IOMMU_for_DMA_Protection_in_UEFI.pdf
Security updates for Intel NUC firmware (INTEL-SA-00084)
Intel ID: INTEL-SA-00084
Product family: Intel® NUC Kits
Impact of vulnerability: Elevation of Privilege
Severity rating: Critical
Original release: Oct 06, 2017
This update improves protection against mitigates multiple vulnerabilities related to security features in Intel® NUC system firmware (BIOS). BIOS Administrator and User password bypass: Insufficient protection of password storage in system firmware for NUC7i3BNK, NUC7i3BNH, NUC7i5BNK, NUC7i5BNH, NUC7i7BNH versions BN0049 and below allows local attacker to bypass Administrator and User passwords via access to password storage. SPI Write Protection Bypass: Insecure platform configuration in system firmare for NUC7i3BNK, NUC7i3BNH, NUC7i5BNK, NUC7i5BNH, NUC7i7BNH versions BN0049 and below allows an attacker with physical presence to run arbitrary code via unauthorized firmware modification during BIOS Recovery. SMM Privilege Elevation: Insufficient input validation in system firmware for Intel® NUC systems allows local attacker to execute arbitrary code via manipulation of memory. Boot Guard Bypass: Incorrect policy enforcement in system firmware for Intel® NUC systems allows attacker with local or physical access to bypass enforcement of integrity protections via manipulation of firmware storage. Dangerous SPI Opcode Protections: Insufficient policy enforcement in system firmware for Intel® NUC systems allows attacker with local or physical access to violate integrity or availability of nonvolatile storage for firmware via specially crafted accesses to nonvolatile storage. Intel highly recommends that users update to the latest version. Intel would like to thank Nikolaj Schlaj for reporting CVE-2017-5700 and CVE-2017-5701 and working with us on coordinated disclosure. Intel would like to thank Embedi for reporting CVE-2017-5721 and CVE-2017-5722 and working with us on coordinated disclosure.[…]
https://security-center.intel.com/advisory.aspx?intelid=INTEL-SA-00084&languageid=en-fr
DMTF Releases Redfish 2017.2
[…]Version 2017.2 of the Redfish Schema and version 1.3.0 of the Redfish Specification are now available for public download. The goal of Redfish is to publish a standard API to meet customer demands for simple and secure management in modern Software Defined Data Center (SDDC) environments, and it was recently announced the standard is being expanded to address Data Center Infrastructure Management (DCIM), as well. The latest release includes updates to the Base Message Registry and more.[…]
http://www.dmtf.org/standards/redfish
http://redfish.dmtf.org/
http://www.dmtf.org/standards/spmf
http://www.dmtf.org/content/dmtf-and-green-grid-address-power-and-cooling
Click to access Redfish_2017_Release_2_Overview.pdf
Note to DMTF PR team: please stop inserting “(http://www.dmtf.org/standards/redfish)” URL after every use of “Redfish”, half a dozen times per paragraph is more than enough.
local press story on Eclypsium
Apple EFI malware triad: Mojo/Thor/Loki?
https://twitter.com/osxreverser/status/916404934462939136
https://twitter.com/osxreverser/status/916405321056309249
https://twitter.com/osxreverser/status/916405109617319936
https://twitter.com/osxreverser/status/916473582720638982
Mojo / Thor / Loki are a triad of malware that infects the EFI of Apple MacBooks.[…]
Embedi: Bypassing Intel Boot Guard
https://twitter.com/_embedi_/status/915974703772205056
In recent years, there is an increasing attention to the UEFI BIOS security. As a result, there are more advanced technologies created to protect UEFI BIOS from illegal modifications. One of such technologies is Intel Boot Guard (BG) – a hardware-assisted BIOS integrity verification mechanism available since Haswell microarchitecture (2013). So-called «UEFI rootkits killer» this technology is designed to create a trusted boot chain (where a current boot component cryptographically measures/verifies the integrity of the next one) with Root-of-Trust locked into hardware.[…]
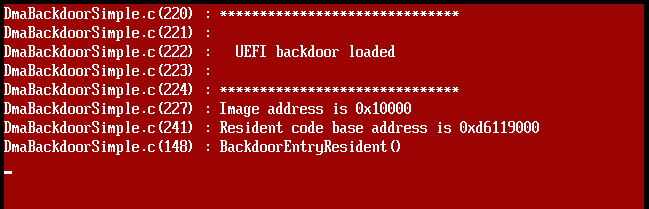
PCI Express DIY hacking toolkit
This repository contains a set of tools and proof of concepts related to PCI-E bus and DMA attacks. It includes HDL design which implements software controllable PCI-E gen 1.1 endpoint device for Xilinx SP605 Evaluation Kit with Spartan-6 FPGA. In comparison with popular USB3380EVB this design allows to operate with raw Transaction Level Packets (TLP) of PCI-E bus and perform full 64-bit memory read/write operations. It’s early version of my first much or less complicated FPGA project, so the speed is quite slow (around 1-2 Mb/s), but in upcoming releases it will be significantly increased by connecting PCI-E endpoint to MicroBlaze soft processor with AXI DMA engine. However, even such low speed is more than enough for reliable implementation of various practical attacks over PCI-E bus: to demonstrate applied use cases of the design, there’s a tool for pre-boot DMA attacks on UEFI based machines which allow executing arbitrary UEFI DXE drivers during platform init. Another example shows how to use pre-boot DMA attacks to inject Hyper-V VM exit handler backdoor into the virtualization-based security enabled Windows 10 Enterprise running on UEFI Secure Boot enabled platform. Provided Hyper-V backdoor PoC might be useful for reverse engineering and exploit development purposes, it provides an interface for inspecting of hypervisor state (VMCS, physical/virtual memory, registers, etc.) from guest partition and perform the guest to host VM escape attacks.
https://github.com/Cr4sh/s6_pcie_microblaze
kernelstub
Ian Santopietro of System76 has a Python-based tool called kernelstub, which boots Linux using the Linux Stub bootloader instead of an external bootloader.
Kernelstub is a basic program enabling booting from the kernel’s built-in EFI Stub bootloader. It keeps the ESP and NVRAM up to date automatically when the kernel updates and allows for modifying and setting the boot parameters/kernel options stored in NVRAM. Kernelstub is a basic program enabling booting from the kernel’s built-in EFI Stub bootloader. It keeps the ESP and NVRAM up to date automatically when the kernel updates and allows for modifying and setting the boot parameters/kernel options stored in NVRAM. It works by detecting certain information about the running OS, kernel, storage devices, and options, then combines all of that together into a unified entity, then calls efibootmgr to register the kernel with the NVRAM. It also copies the latest kernel, initrd.img to the EFI System Partition so that UEFI can find it. It will also store a copy of the kernel’s command line (/proc/cmdline) on the ESP in case of necessary recovery from an EFI shell.
https://launchpad.net/kernelstub
He just gave a talk/demo of it at SeaGL:
https://osem.seagl.org/conferences/seagl2017/program/proposals/326
His presentation mentioned this blog in the ‘more info’ slide! 🙂
Intel SGX tutorial, part 10
Intel has a new tutorial on Intel SGX, part 10.
Duo releases EFIgy
Duo Labs has released a new open source tool to help Apple Mac users check their EFI release!
OSdev.org ACPI articles
I just noticed that osdev.org has some wiki pages on ACPI, and the FADT entry has been recently been updated. It is nice to have another source of ACPI information. 🙂
Ekoparty presentation by Eclypsium available
AMI announces full Redfish 1.0 support
American Megatrends Announces Full Support for Redfish™ 1.0 Specification in Aptio® V UEFI BIOS and MegaRAC® BMC Remote Management Firmware
Monday: October 2, 2017
AMI has announced its full support for the Redfish™ 1.0 specification from the Distributed Management Task Force (DMTF), in both its Aptio® V UEFI BIOS Firmware as well as several products within the MegaRAC® Manageability Framework – the most widely used solution in the market today. […] In addition to its industry-leading Aptio® V UEFI BIOS Firmware, known and trusted by Tier One OEMs and ODMs around the globe, products from AMI featuring support for Redfish 1.0 include the fully-integrated MegaRAC Pooled System Management Engine (PSME) firmware solutions, which enable efficient resource management for Network, Storage and Compute hardware throughout the data center, as well as MegaRAC Composer™ Pod Management Software.[…]
https://ami.com/en/products/remote-management/rack-scale-design-solutions/.
Baidu updates Rust SGX SDK
Re: https://firmwaresecurity.com/2017/07/23/baidu-releases-sgx-sdk-for-rust/
Baidu has updated their Rust SDK for Intel SGX:
https://github.com/baidu/rust-sgx-sdk/releases/tag/v0.9.0
Agenda for ECC’17
The schedule for the European Coreboot Conference 2017 (ECC’17) is out:
* Keynote, Stefan Reinauer
* Run upstream coreboot on an ARM Chromebook. Paul Menzel
* DDR3 memory initialization basics on Intel Sandybrige platforms. Patrick Rudolph
* Booting UEFI-aware OS on coreboot enabled platform – “In God’s Name, Why?”. Piotr Król, Kamil Wcisło
* Reverse engineering MT8173 PCM firmwares and ISA for a fully free bootchain. Paul Kocialkowski
* Let’s move SMM out of firmware and into the kernel. Ron Minnich
* A Tale of six motherboards, two BSDs and coreboot. Piotr Kubaj
* Buying trustworthy hardware for federal agencies: How open source firmware saves the day. Carl-Daniel Hailfinger
* SINUMERIK 840D sl – step ahead with coreboot. Werner Zeh
* Enabling TPM 2.0 on coreboot based devices Piotr Król, Kamil Wcisło
* Reverse Engineering x86 Processor Microcode. Philipp Koppe, Benjamin Kollenda
* Porting coreboot to the HP ProLiant MicroServer Gen8. Alexander Couzens, Felix Held
* Implementing coreboot in a ground breaking secure system: ORWL. Wim Vervoorn , Gerard Duynisveld
VisualUEFI udpated
more on Google NERF
Google NERF looks interesting, they keep UEFI’s PI but replace the UEFI layers with Linux kernel, and the code is written in Go. Looks like they’re focusing on removing dynamic code in UEFI and SMM. Unclear about their position towards dynamic code in ACPI, as well as PCIe (eg, PCIleech-style attacks).
The slides from the recent North American OSS presentation are online, but I can’t find the video online:
Click to access Linuxcon%202017%20NERF.pdf
There’s an upcoming European OSS event upcoming:
Replace Your Exploit-Ridden Firmware with Linux
Ronald Minnich, Google
With the WikiLeaks release of the vault7 material, the security of the UEFI (Unified Extensible Firmware Interface) firmware used in most PCs and laptops is once again a concern. UEFI is a proprietary and closed-source operating system, with a codebase almost as large as the Linux kernel, that runs when the system is powered on and continues to run after it boots the OS (hence its designation as a “Ring -2 hypervisor”). It is a great place to hide exploits since it never stops running, and these exploits are undetectable by kernels and programs. Our answer to this is NERF (Non-Extensible Reduced Firmware), an open source software system developed at Google to replace almost all of UEFI firmware with a tiny Linux kernel and initramfs. The initramfs file system contains an init and command line utilities from the u-root project (http://u-root.tk/), which are written in the Go language.
https://osseu17.sched.com/event/ByYt/replace-your-exploit-ridden-firmware-with-linux-ronald-minnich-google
https://ossna2017.sched.com/event/BCsr/replace-your-exploit-ridden-firmware-with-linux-ronald-minnich-google
https://osseu17.sched.com/event/ByYt/replace-your-exploit-ridden-firmware-with-linux-ronald-minnich-google
http://u-root.tk/
https://github.com/u-root/u-root
more from Duo on Apple EFI security
Nice, in addition to an upcoming new EFI tool, it appears Duo has some defensive advise, using OSQuery, Puppet, and Chef. Click on the first tweet below for an image from their upcoming presentation.
Note that Teddy Reed is giving a presentation on OSQuery in November at Usenix LISA:
Pepjin’s Apple EFI version spreadsheet:
https://docs.google.com/spreadsheets/d/1qGRVF1aRokQgm_LuTsFUN2Knrh0Sd3Gp0ziC_VIWqoM/edit#gid=0
Google Titan trust paper available
A Vendor-Agnostic Root of Trust for Measurement
Jon McCune, Rick Altherr
We report the success of a project that Google performed as a proof-of-concept for increasing confidence in first-instruction integrity across a variety of server and peripheral environments. We begin by motivating the problem of first-instruction integrity and share the lessons learned from our proof-of-concept implementation. Our goal in sharing this information is to increase industry support and engagement for similar designs. Notable features include a vendor-agnostic capability to interpose on the SPI peripheral bus (from which bootstrap firmware is loaded upon power-on in a wide variety of devices today) without negatively impacting the efficacy of any existing vendor- or device-specific integrity mechanisms, thereby providing additional defense-in-depth.
https://research.google.com/pubs/pub46352.html
Yuriy of Eclypsium has a few comments on the doc, click on below tweet for thread:

You must be logged in to post a comment.