https://twitter.com/esden/status/959871470192148480
https://www.crowdsupply.com/sifive/hifive-unleashed
https://abopen.com/news/multi-core-64-bit-linux-capable-risc-v-board-unveiled-available-pre-order/
Boot Shim is a small ARM32 Windows Boot Manager Application that intended to chain-load the normal UEFI environment for UEFI application development on hacked Lumias. As Lumia verifies bootarm.efi or whatever on initialization even when Secure Boot is turned off, this application can provide additional image load capabilities, but you have to develop it from the framework provided.[…]
https://www.hex-rays.com/products/ida/support/download_freeware.shtml
The freeware version of IDA v7.0 has the following limitations:
no commercial use is allowed
lacks all features introduced in IDA > v7.0
lacks support for many processors, file formats, debugging etc…
comes without technical support
European embedded Linux company Free Electrons renames to Bootlin.
AFAICT they have not changed their Github account name.
https://github.com/free-electrons
From Linaro Connect 2017 in San Francisco:
Digital signatures and the beginning of the world – SFO17-306
David Brown
The bootloader is where it all begins. This session sums up our experiences with various signature types, data formats, implementations and how to choose.
http://connect.linaro.org/resource/sfo17/sfo17-306/
The microarchitecture of Intel, AMD and VIA CPUs
An optimization guide for assembly programmers and compiler makers
By Agner Fog. Technical University of Denmark.
Copyright © 1996 – 2017. Last updated 2017-05-02.
Click to access microarchitecture.pdf
Qubes OS 4.0-rc4 has been released!
Jan 31, 2018 by Andrew David Wong in Releases
We’re pleased to announce the fourth release candidate for Qubes 4.0! This release contains important safeguards against the Spectre and Meltdown attacks, as well as bug fixes for many of the issues discovered in the previous release candidate.[…]
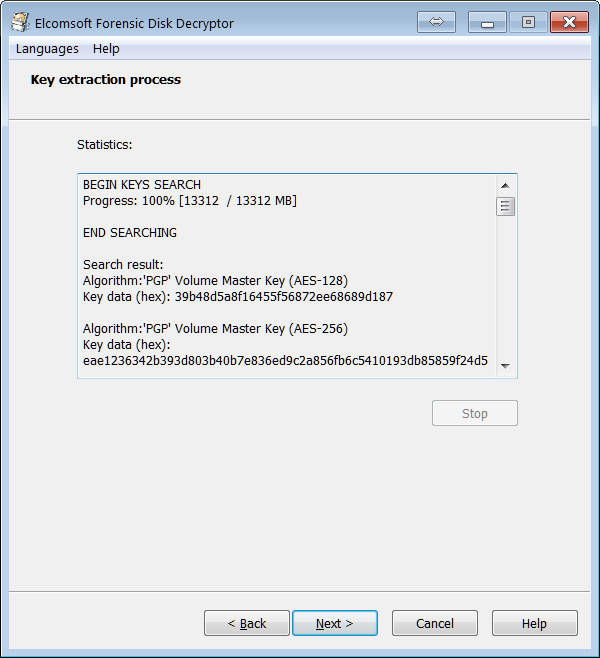
How to Instantly Access BitLocker, TrueCrypt, PGP and FileVault 2 Volumes
January 31st, 2018 by Vladimir Katalov
It’s been a long while since we made an update to one of our most technically advanced tools, Elcomsoft Forensic Disk Decryptor (EFDD). With this tool, one could extract data from an encrypted disk volume (FileVault 2, PGP, BitLocker or TrueCrypt) by utilizing the binary encryption key contained in the computer’s RAM. We could find and extract that key by analyzing the memory dump or hibernation files. What Elcomsoft Forensic Disk Decryptor did not do until now was pretty much everything else. It couldn’t use plain text passwords to mount or decrypt encrypted volumes, and it didn’t support escrow (recovery) keys. It didn’t come with a memory imaging tool of its own, making its users rely on third-party solutions. With today’s release, Elcomsoft Forensic Disk Decryptor gets back on its feets, including everything that was missing in earlier versions. Plain text passwords and recovery keys, a Microsoft-signed kernel-level RAM imaging tool, the highly anticipated portable version and support for the industry-standard EnCase .E01 and encrypted DMG images are now available. But that’s not everything! We completely revamped the way you use the tool by automatically identifying all available encrypted volumes, and providing detailed information about the encryption method used for each volume.[…]
https://www.elcomsoft.com/efdd.html
iExtractor: Automate Extraction from iOS Firmware Files
iExtractor is a collection of tools and scripts to automate data extraction from iOS firmware files (i.e. IPSW files). It runs on macOS and partially on Linux (certain tools and features only work on macOS). IPSW (iPhone Software) files are provided publicly by Apple for OTA (over-the-air) updates for devices running iOS. ipsw.me provides links to IPSW files by device and iOS version. Similar information is on The iPhone Wiki. IPSW files are ZIP files packing the filesystem, kernel image and other files. The filesystem image and kernel image files for iOS <= 9 are encrypted; the firmware keys for most of these files are provided by the community on The iPhone Wiki. In the command output below 058-25512-331.dmg (the largest file) is the filesystem image file and kernelcache.release.n41 is the kernel image file or the kernelcache.[…]
https://github.com/malus-security/iExtractor
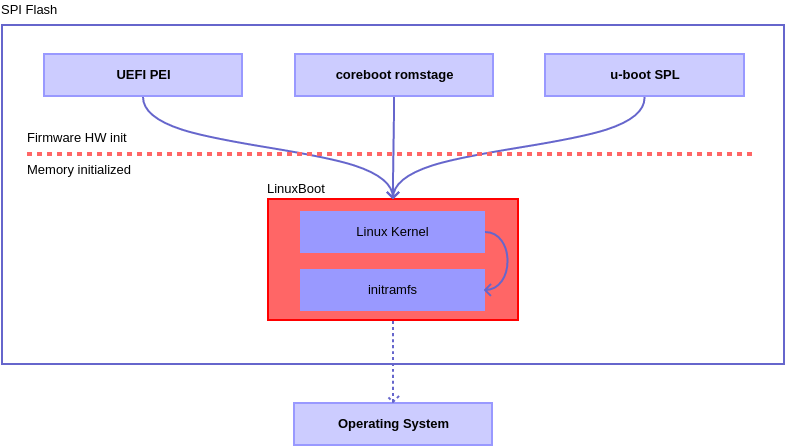
LinuxBoot has a new Twitter account, and their web site is pretty new as well.
https://twitter.com/TinyFPGA/status/958572873043664896
https://github.com/tinyfpga/TinyFPGA-Bootloader
“An open source USB bootloader for FPGAs”
https://security-center.intel.com/advisory.aspx?intelid=INTEL-SA-00086&languageid=en-fr
Acknowledgements: External Security Researchers and Intel Validation. Intel would like to thank Mark Ermolov and Maxim Goryachy from Positive Technologies Research for working collaboratively with Intel on a coordinated disclosure and providing the initial finding for CVE-2017-5705, CVE-2017-5706 and CVE-2017-5707.
Linux Kernel Runtime Guard (LKRG) is a loadable kernel module that performs runtime integrity checking of the Linux kernel and detection of security vulnerability exploits against the kernel. As controversial as this concept is, LKRG attempts to post-detect and hopefully promptly respond to unauthorized modifications to the running Linux kernel (integrity checking) or to credentials (such as user IDs) of the running processes (exploit detection). For process credentials, LKRG attempts to detect the exploit and take action before the kernel would grant the process access (such as open a file) based on the unauthorized credentials. There’s a mailing list where you can share your experience with LKRG and ask questions.[…]
One more thing to add to above list:
You could maintain the apparently abandoned Lua port to UEFI.
Starting From Scratch: Trusted Root in Samsung Mobile Devices
Jan 26, 2018 by Joel Snyder
Android’s decoupling of the hardware and operating system brings benefits to IT: It allows application and hardware vendors to compete on innovation, features, form factor, price and security. Samsung Knox is an example of the latter: A combination of hardware features and software enhancements to Android that increase mobile security. Not every Android phone is designed for the enterprise market. Vendors such as Samsung have evaluated the higher security requirements of enterprise customers and have responded by releasing trusted platforms: Devices with built-in hardware that establishes the integrity and identity of the platform and ensures only trusted software is loaded. With a trusted platform, bootkit and rootkit attacks by malware and curious end users are generally blocked. Additionally, data encryption is more difficult to subvert because keys are not software accessible. Today’s technology comes from the Trusted Computing Group (TCG) which publishes the Trusted Platform Module (TPM). TCG started in 2003, defining what a trusted platform would look like, and how it might be implemented and standardized. A TPM is a computer-within-a-computer, completely shielded from the main CPU. Software, whether friendly or unfriendly, can’t reach into the memory or storage of the TPM directly. In larger devices, such as laptops and desktops, the TPM is usually a separate chip.[…]
Starting From Scratch: Trusted Root in Samsung Mobile Devices
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Discover the Desktop
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
News from coreboot world
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Just another WordPress.com site
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
You must be logged in to post a comment.