A miniemulator of UEFI firmware in Mac OSX.
I wanna create a emulator base on tiano UDK2015 which can be run in Mac OSX.
https://github.com/efikarl/liano
see-also:
A miniemulator of UEFI firmware in Mac OSX.
I wanna create a emulator base on tiano UDK2015 which can be run in Mac OSX.
https://github.com/efikarl/liano
see-also:
Fall 2017 UEFI Plugfest – October 30-November 3, 2017
State of the UEFI – Mark Doran (UEFI Forum President)
UEFI Security Response Team (USRT) – Dick Wilkins (UEFI Forum)
“Last Mile” Barriers to Removing Legacy BIOS – Brian Richardson (Intel)
UEFI Firmware Security Concerns and Best Practices – Dick Wilkins (Phoenix)
Strategies for Stronger Software SMI Security in UEFI Firmware – Tim Lewis (Insyde)
UEFI in Arm Platform Architecture – Dong Wei (ARM)
Self-Certification Tests (SCTs) in UEFI World – Eric Jin (Intel) and Alex Hung (Canonical)
Firmware Test Suite -Uses, Development, Contribution and GPL – Alex Hung (Canonical)
Near Field Communication (NFC) and UEFI – Tony Lo (AMI)
EDK2 Platforms Overview – Leif Lindholm (Linaro)
UEFI Manageability and REST Services – Abner Chang (HPE) and Ting Ye (Intel)
Intel Hardware Accelerated Execution Manager (HAXM)
HAXM is a hardware-assisted virtualization engine (hypervisor) that uses Intel Virtualization Technology to speed up IA (x86/ x86_64) emulation on a host machine running Windows or macOS. It started as an Android SDK component, but has recently transformed itself into a general accelerator for QEMU. HAXM can be built as either a kernel-mode driver for Windows or a kernel extension for macOS.[…]
See-also:
https://01.org/android-ia/q-and-a/what-haxm
https://software.intel.com/en-us/articles/intel-hardware-accelerated-execution-manager-intel-haxm
Current Purism Librem15 systems — based on Intel x64/coreboot/SeaBIOS tech — results in 3 FAILs and 1 WARNING from CHIPSEC:
The UEFI Forum recommends that OEMs pass CHIPSEC’s tests before shipping units to customers. I wish modern BIOS-based OEMs would also heed that advice… The default install is to use an MBR-based partition, so also be wary of all of the existing BIOS-centric, MBR-based rootkits. Adhere all ‘evil maid’ warning signs with this laptop. If you have corporate policies that require NIST 800-147/155/193 requirements, you might have to work hard to justify this device. I wish it were not true: configurable or secure, choose one.
In other computer review news: the trackpad did not work during initial install, had to be rebooted. I’m guessing trackpad drivers aren’t integrated? You’ll have to use external mouse if you need to click on something during install of Linux. Same with backlit key and display intensity features: only worked after OS setup. Firmware security pedantry aside, nice hardware. Fan rarely kicks in, unlike some OEMs. It is nice to see a Mac-style trackpad instead of a PC-style touchpad with 2 explicit button areas, I’ve grown to dislike those. Startup and poweroff are both very fast. Reminds me of what a modern non-UEFI system should be like. Great, except we’re no longer in a world where security can be ignored. If you want an insecure BIOS box, you’ll probably enjoy this system. If you care about security, this is a BIOS box….
AMI has a new blog post with an introduction to TPM, and some links for more info on TPMs.
[…] Led by National Security Agency (NSA) alumni, ReFirm Labs aims to close the firmware security gap exploited by hackers to gain control of or disable IoT devices such as digital cameras, home appliances, routers, servers, printers and other connected machines. These common devices can be remotely taken over, destroyed or hijacked for Botnet attacks that effectively shut down or slow major web services such as Twitter, Spotify, Netflix, and PayPal. Distributed denial of service (DDoS) attacks use infected devices to bombard websites and have cost some organizations as much as $22,000 a minute in lost business and remediation costs. “Manufacturers often have little visibility or control over the firmware of third-party components that are integrated into their devices,” said ReFirm Labs CEO and co-founder Terry Dunlap, an NSA veteran with deep experience in wireless network security. “ReFirm Labs’ Centrifuge Platform makes it possible to rapidly assess the security posture of a device at any point in the lifecycle chain, identifying backdoor accounts, hard-coded passwords and potential zero-day threats.” Other key members of the ReFirm Labs team include co-founder and CTO Peter Eacmen, a Naval Postgraduate School alumni and former Department of Defense cyber expert for the NSA, FBI, and US Special Forces; and Principal Research Engineer Craig Heffner, author of the open source firmware project “binwalk,” a tool for reverse engineering compiled firmware images of embedded systems, and Firmware Mod-Kit. Additionally, John Stewart, Chief Security Officer of Cisco and Jay Emmanuel, Chief Architect at DataTribe, joined the ReFirm Labs board of directors.[…]
https://globenewswire.com/news-release/2017/11/15/1193408/0/en/ReFirm-Labs-Announces-1-5-Million-in-Funding-From-Startup-Studio-DataTribe-and-Launches-Firmware-Validation-Platform.html
https://www.refirmlabs.com/
Palantir has a new blog post on OSquery.
[…]The goal of this blog post is twofold: first, to provide configuration guidance for a multi-platform osquery deployment, and second to describe our open-source set of osquery configurations:[…]
Arg, WordPress messes up medium.com-based URLs. Remove the 2 spaces in the below URL, or click on the URL from the above tweet instead:
https:// medium.com /@palantir/osquery-across-the-enterprise-3c3c9d13ec55
CopperheadOS is “A security and privacy focused mobile operating system compatible with Android apps.“.
It appears the company is having problems trying to monetize an open sourced operating system. I hope they can solve things, they’re doing interesting security things with Android.
https://copperhead.co/android/
https://github.com/copperheados/
Kees Cook has a new blog post, talking about new security features in Linux kernel 4.14.
vmapped kernel stack on arm64
set_fs() balance checking
SLUB freelist hardening
setuid-exec stack limitation
randstruct automatic struct selection
structleak passed-by-reference variable initialization
improved boot entropy
eBPF JIT for 32-bit ARM
seccomp improvements
Plato updates ME Analyzer, and an Intel microcode document!
https://github.com/platomav/MEAnalyzer
https://github.com/platomav/MCExtractor/wiki/Intel-Microcode-Extra-Undocumented-Header
The Arm Architecture is continually evolving, and this blog gives a high-level overview of some of the changes made in Armv8.4-A*. We develop these changes by listening to the Arm Ecosystem and working with them to provide new functionality that benefits everyone. These are incremental changes to the architecture and do not introduce any significant new features. Previous incremental versions of the architecture have been introduced for v8.3-A, v8.2-A, and v8.1-A. The rest of this blog introduces some of the new functionality. It does not offer a complete feature list. However, over the next few months we will be describing this functionality in more detail.[…]
ARM Assembly Basics Cheatsheet
This ARM assembly basics cheatsheet covers registers, instructions, branching, and conditional execution. You can use it as a guideline if you’re starting out with ARM assembly and need a little refresher of the basics.
If you write C/C++ code, here’s a new blog to start watching:
Hardening C/C++ Programs Part II – Executable-Space Protection and ASLR
Here are two more tools that convert to or from UEFI image formats to other formats. There are a handful of others.
elf2efi: convert statically linked ELF binaries to PE images for UEFI
https://github.com/efidroid/modules_elf2efi
PEIUtil: Tool to convert UEFI images from PEI (TE or VZ files) to PE for analysis.
https://github.com/rickmark/peiutil
edk2-trace: Proof-of-concept user space application for stack trace support in UEFI on x64 platforms. The PE/COFF executable basically prints out call stack information at runtime.
Dependencies: x64 platform, GNU make, MinGW toolchain, Wine (if you’re using Linux)
https://github.com/pcacjr/edk2-trace
FOSDEM is happening in Brussels, Belgium in early February.
FOSDEM Hardware Enablement Devroom Call for Participation
In this devroom we want to discuss topics surrounding hardware enablement. Subjects can range from the firmware running on the bare metal machine, drivers and plumbing all the way to the user interface. We welcome a board range of presentations, including but not limitied to technical talks, state of union summaries as well as discussions that facilitate the collaboration between community members, software vendors and OEMs. A particular emphasis will be given to talks covering a significant part of the software stack involved in hardware enablement, with an obvious focus on using open source throughout the whole stack.
Topics & Examples
* UX design to enable users to use their HW effectively
* Firmware:
– coreboot
– flashrom
– UEFI EDK2 (Tianocore)
– Security
– Lockdown of platform using firmware
– Updating
* Secure Boot
* Hardware testing / certification
* Thunderbolt 3 security modes
* Gaming input devices (keyboards, mice, piper)
* Biometric authentication
* Miracast or controlling remote devices
* Why vendors should facilitate upstream development
There are many more devrooms, as well:
https://fosdem.org/2018/news/2017-10-04-accepted-developer-rooms/
The efidroid project is working on a new toolchain for UEFI. Tianocore’s build environment is strange enough that it is hard to use outside Tianocore, like when a distro needs to build a .efi binary, for example.
crosstool-ng project for UEFI
Crosstool-NG config and patches for building a UEFI toolchain
Michał Kowalczyk has an interesting presentation on Intel BIOS reversing, focusing on a Toshiba system. Presentation is in Polish. If you have a Toshiba, see the excerpt below with advisory info.
https://twitter.com/q3k/status/928672822808973312
Oficjalne stanowisko Toshiby
Toshiba is working on a temporary BIOS update that can be used to prevent the security issue that has been raised and expects to release this update on its website within the next 2 weeks.
Toshiba plans to start the release of a permanent fix for some models from January, 2018 and will complete the releases of permanent fix for all applicable models by the end of March 2018.
Click to access bd81619010b3b8ef012ff8af491a034bd9c6c3adfd76ddbb180c43c15f291fc1.pdf
Wow, amazing!
Inside a low budget consumer hardware espionage implant
Analysis of the S8 data line locator
mich @0x6d696368
The following analysis was performed on a S8 data line locator […]A while back Joe Fitz tweeted about the S8 data line locator1. He referred to it as “Trickle down espionage” due to its reminiscence of NSA spying equipment. The S8 data line locator is a GSM listening and location device hidden inside the plug of a standard USB data/charging cable. It supports the 850, 900, 1800 and 1900 MHz GSM frequencies. Its core idea is very similar to the COTTONMOUTH product line by the NSA/CSS [1] in which an RF device is hidden inside a USB plug. Those hidden devices are referred to as implants. The device itself is marketed as a location tracker usable in cars, where a thief would not be able to identify the USB cable as a location tracking device. Its malicious use-cases can, however, not be denied. Especially since it features no GPS making its location reporting very coarse (1.57 km deviation in my tests). It can, e.g., be called to listen to a live audio feed from a small microphone within the device, as well as programmed to call back if the sound level surpasses a 45 dB threshold. The fact that the device can be repackaged in its sliding case, after configuring it, i.e. inserting a SIM, without any noticeable marks to the packaging suggests its use-case: covert espionage.[…]
I was not able yet to write new firmware via flashrom because I was not able to disable block protection on the flash, yet. Maybe a different avenue for flashing new firmware could be the SPFlash tool4 and/or the Flash tool. However, that would not be open source. If know something about the weird FAT12 file system used in the device or are able to flash your S8 data line locator please contact me with details![…]
No writeup would be complete without at least one fuck up. So here it is: While using the S8 data line locator with OpenBTS I provisioned imaginary numbers. When switching SIM cards I forgot to turn of the voice activated callback. So long story short, some guy with the number 3333333 listend in on me for 2 minutes:
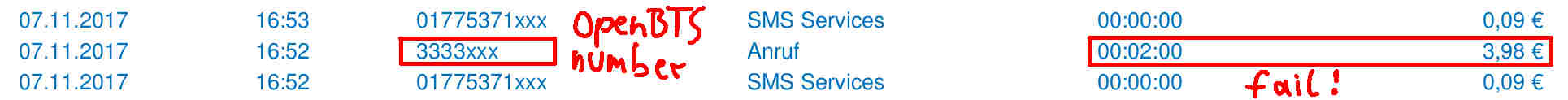 Provider call log fail. I did not notice this until I reviewed the logs! So my resume on these little hardware espionage implants: They are stealthy and dangerous as fuck![…]
Provider call log fail. I did not notice this until I reviewed the logs! So my resume on these little hardware espionage implants: They are stealthy and dangerous as fuck![…]
This is a new project, a C# GUI that requires Windows and Visual Studio to build. It appears to be a wrapper to the Windows shutdown.exe utility.
https://github.com/spoonieau/Restart2UEFI
Restart2UEFI: Utility’s to restart uefi systems to firmware. An easyer way to get your system to boot to the motherboards firmware interface than going Win’s recovery options, to finding a pappercilp the certain notebooks.
Restart2UEFI winforms build ported to UWP. Needs Restart2UEFIHelper.exe in projects win32 dir. Was going to be release on the windows store but due to needing the use of a win32exe and only holding a developer licence. So I was unable to submit and have a compiled App available.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Discover the Desktop
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
News from coreboot world
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Just another WordPress.com site
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
You must be logged in to post a comment.