Steve McIntyre has updated the Debian wiki page for Secure Boot “to cover a lot more user-facing stuff.”
GRUB2 security changes in Fedora
[…]Include Grub’s “verify,” “cryptodisk,” “luks” and <others here> modules in grubx64.efi of the ‘grub2-efi-x64’ package. Users utilising secure boot functionality on the UEFI platform cannot insert modules that aren’t in grubx64.efi. Paradoxically, this means that security-conscious users cannot use grub’s verify module, or employ (near) full disk encryption using cryptodisk and luks. The security benefits of signature verification would reach more users if Fedora automated it by incorporating the process into grub2-mkconfig. For the long-term, to grant flexibility with grub2 modules on secure boot instances, it may be advisable to sign the .mod files in the ‘grub2-efi-x64-modules’ package, modify grub2-mkconfig (or -install) to copy the necessary modules into the EFI partition when required by the user’s configuration and then allow inserting of signed modules in secure boot instances.[…]
https://fedoraproject.org/wiki/Changes/Include_security_modules_in_efi_Grub2
https://www.phoronix.com/scan.php?page=news_item&px=GRUB2-New-EFI-Modules-For-F31
Down the Rabbit Hole blog, part 3 posted
MAC address of targets of ASUS ShadowHammer attack
Positive Technologies: Intel VISA: Through the Rabbit Hole, slides available
PoC||GTFO 0x19 released
Open Source Firmware track at LinuxFestNorthWest 2019
LinuxFestNorthWest.org is the annual Linux conference for Washington state and the Pacific NorthWest area. This year, there’s an “Open Source Firmware” track, for the first time.
UEFI Boot for Mere Mortals
Why Open Source is Critical For Platform Firmware
Defending Out-of-Band Management Attacks
Network Boot in a Zero-Trust Environment
Open-Source Host Firmware Directions
The Fight for a Secure Linux BIOS… Past, Present and Future
https://www.linuxfestnorthwest.org/conferences/2019/schedule/events
https://www.linuxfestnorthwest.org/conferences/2019
Spring 2019 UEFI Plugfest: schedule announced
State of the UEFI Forum
UEFI Self Certification Tests (UEFI-SCT) and Firmware Test Suite (FWTS)
UEFI Updates and Open Source Firmware evolutions on Arm
10:30 Risks to UEFI firmware due to growing attack surfaces
From Runtime to Compile Time: Improving ASL Through Enhanced Namespace Resolution
Microsoft UEFI Update
Hardening Firmware Components with Host-based Analysis
Half Duplex controller support and Multi IO support in SPI framework
Improving UEFI Network Stack Performance
Case Study: Removing SMM from Intel Platforms
Support Secure UEFI and OPTEE OS together on Arm
Role Modeling Open Source Best Practices in Firmware
Using Capsules for Firmware Configuration Update
UEFI topics for the manufacturing efficiency/second half hour of lunch
How Writing Portable UEFI Drivers Improves Reliability (and Helps Me)
Redfish Implementation for UEFI
Redfish Host Interface: UEFI and OS implications
Click to access 2019%20Spring%20Schedule%2027March%202019%20final.pdf
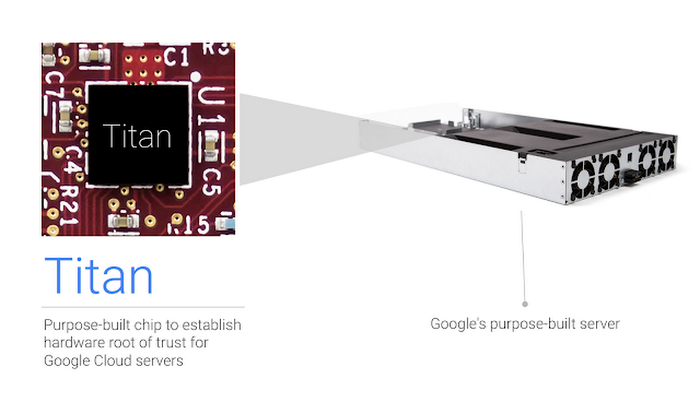
Google: Mitigating risk in the hardware supply chain
Google has a new blog post talking about supply-chain security and their Titan chip.
[…]One area where we’ve put a lot of thought, and which we continue to focus on, is the security of our hardware supply chain. Today, I’d like to go into a few of the things we do specifically in this area.[…]
bcdedit-revert-uefi-gpt-boot-order: Powershell script to modify the UEFI/GPT boot order
This powershell script modifies the UEFI/GPT boot order by finding the first non-Windows entry and moving it to the top of the order. When using UEFI+GPT, the Windows installation (since Windows 7?) creates its own boot device entry (“Windows Boot Manager”, a.k.a. “{bootmgr}”) in the UEFI/GPT boot order list and, obnoxiously, takes the liberty of moving said entry to the top of the list. Under most circumstances, this is fine, and probably desirable. However for systems used for repeated deployment testing, or systems which you want a different bootloader to take priority (such as dual-boot systems, or computer lab systems that can be remotely re-imaged), this is a show stopper. So I needed a way to do this programmatically. This script makes use of the arcane and undocumented {fwbootmgr} identifier implemented by bcdedit to find the first non-Windows boot device entry in the UEFI/GPT boot order list and move it to the top of the list.
https://github.com/mmseng/bcdedit-revert-uefi-gpt-boot-order
Automating Firmware Security with FwAnalyzer
Looking forward to seeing what FwAnalyzer is about!!
by Collin Mulliner – Cruise Automation
Modern devices are complex and their firmware often consists of multiple parts that together make up the software stack of the product. Securing firmware is a lot of work and even basic issues can cause a lot of pain in the long run. Firmware changes over time and is built for different purposes such as development, testing, and production. Simple but bad changes can have a huge effect if put into production catching those changes before shipping or even during development can prevent a lot of issues.
This talk is about FwAnalyzer, a tool to analyze filesystem images for security issues. Analysis is based on configurable rules that model things such as file ownership, permissions, and file content. FwAnalyzer further provides a data extraction engine that is used to gather information from a filesystem and make it accessible via its machine readable report. Overall FwAnalyzer is built to be used by experts for security analysis of existing firmware and for integrating it into the build pipeline to provide direct feedback during development. The talk is based on our experience of dealing with firmware for Linux-based devices built in-house and developed by 3rd parties.
NoStarch: Rootkits and Bootkits has shipped to the printer
Linux Foundation adopts the LVFS Project
The Linux Foundation welcomes the Linux Vendor Firmware Service (LVFS) as a new project. LVFS is a secure website that allows hardware vendors to upload firmware updates. It’s used by all major Linux distributions to provide metadata for clients, such as fwupdmgr, GNOME Software and KDE Discover. To learn more about the project’s history and goals, we talked with Richard Hughes, upstream maintainer of LVFS and Principal Software Engineer at Red Hat.[…]
https://www.linuxfoundation.org/blog/2019/03/lvfs-project-announcement/
https://www.linux.com/news/linux-foundation-welcomes-lvfs-project
see-also:
https://github.com/hughsie/fwupd
https://fwupd.org/lvfs/devicelist
ASUS releases diagnostic tool for Windows
Re: https://firmwaresecurity.com/2019/03/25/asus-live-update-utility-security-issues/
https://www.asus.com/News/hqfgVUyZ6uyAyJe1
[…]Additionally, we have created an online security diagnostic tool to check for affected systems, and we encourage users who are still concerned to run it as a precaution. The tool can be found:
https://dlcdnets.asus.com/pub/ASUS/nb/Apps_for_Win10/ASUSDiagnosticTool/ASDT_v1.0.1.0.zip
A second CHIPSEC GUI
The first CHIPSEC GUI I knew about was chipsec_gui. This one has Persian and English UIs.
https://github.com/EmadHelmi/chipsec_gui
Now there is another CHIPSEC GUI, called CHIPSEC-GUI.
https://github.com/SoheilKhodayari/CHIPSEC-GUI
Both are PyQt-based. Neither are from the Intel CHIPSEC team, or included with the core CHIPSEC project.
Awesome Windows Rootkits
1-day old, let’s see if it if grows…
EfiGuard: Disable PatchGuard and DSE at boot time
https://github.com/Mattiwatti/EfiGuard
I suspect a legal infringment from MSFT, they have “* Guard” trademarked… 🙂
Airbus Security Lab: Riding the lightning iLO BMC security wrap-up
By: Fabien Perigaud, Alexandre Gazet & Joffrey Czarny
https://airbus-seclab.github.io/
https://insomnihack.ch/conferences/
See-also: 
Tenable: BadUSB in routers
CoonBOOT: UEFI x86_64 bootloader written in Rust
UEFI x86_64 bootloader for upcoming CoonOS written in Rust.
Presumably named after the icon of the creator:


You must be logged in to post a comment.