https://github.com/objective-see/DoNotDisturb
https://objective-see.com/products/dnd.html

Command Line EFI Mounter
This is a simple app that helps you to mount any EFI partition Inside Mac OS X.
Working for Mac OS X 10.9 to 10.13
https://github.com/chris1111/Command-Line-EFI-Mounter
macOS Shell Scripts to clone the EFI partition automatically from either Carbon Copy Cloner or SuperDuper! when run on a Hackintosh
https://github.com/wombat94/EFIClone
This Mac-centric bash script has been rewritten as a Mac-centric Python script:
“A more robust edition of my previous MountEFI script. Added my usual collection of disk functions – plus some experimentation with callback functions.
def custom_quit():
head(“MountEFI”)
print(“by CorpNewt\n”)
print(“Thanks for testing it out, for bugs/comments/complaints”)
print(“send me a message on Reddit, or check out my GitHub:\n”)
print(“www.reddit.com/u/corpnewt”)
print(“www.github.com/corpnewt\n”)
print(“Have a nice day/night!\n\n”)
exit(0)
GUI wrapper for bootoption that creates a bootable (systemd-boot) flash drive for the sole purpose of adding a loader to the firmware menu.
https://github.com/vulgo/Punchdrum

Siguza, 01. Dec 2017 (published 31. Dec 2017)
IOHIDeous
“IOHIDFamily once again.”
This is the tale of a macOS-only vulnerability in IOHIDFamily that yields kernel r/w and can be exploited by any unprivileged user. IOHIDFamily has been notorious in the past for the many race conditions it contained, which ultimately lead to large parts of it being rewritten to make use of command gates, as well as large parts being locked down by means of entitlements. I was originally looking through its source in the hope of finding a low-hanging fruit that would let me compromise an iOS kernel, but what I didn’t know it then is that some parts of IOHIDFamily exist only on macOS – specifically IOHIDSystem, which contains the vulnerability discussed herein.[…]
https://siguza.github.io/IOHIDeous/
https://github.com/Siguza/IOHIDeous/blob/master/docs/index.md
https://github.com/Siguza/iokit-utils
https://github.com/Siguza/hsp4
https://github.com/Siguza/ios-kern-utils
Rick Mark has released efivalidate, a macOS-centric Ruby-based EFI checking tool. Also, by same author, Mojo_Thor project has activity. I thought it was a one-time drop, but it is actively being updated:
efivalidate is a ruby utility to take a given input EFI payload from macOS and to compare it against Apple’s validation schema. Being written in ruby this can occur off-box to ensure that the utility itself hasn’t been compromised
https://github.com/rickmark/efivalidate
Loki / Thor / Mojo are a triad of Apple internal tools and malware that infects the SMC, EFI and macOS of Apple MacBooks. It is believed that direct access to the hardware is gained by re-flashing the Thunderbolt controller (via ThorUtil)
A miniemulator of UEFI firmware in Mac OSX.
I wanna create a emulator base on tiano UDK2015 which can be run in Mac OSX.
https://github.com/efikarl/liano
see-also:
Intel Hardware Accelerated Execution Manager (HAXM)
HAXM is a hardware-assisted virtualization engine (hypervisor) that uses Intel Virtualization Technology to speed up IA (x86/ x86_64) emulation on a host machine running Windows or macOS. It started as an Android SDK component, but has recently transformed itself into a general accelerator for QEMU. HAXM can be built as either a kernel-mode driver for Windows or a kernel extension for macOS.[…]
See-also:
https://01.org/android-ia/q-and-a/what-haxm
https://software.intel.com/en-us/articles/intel-hardware-accelerated-execution-manager-intel-haxm
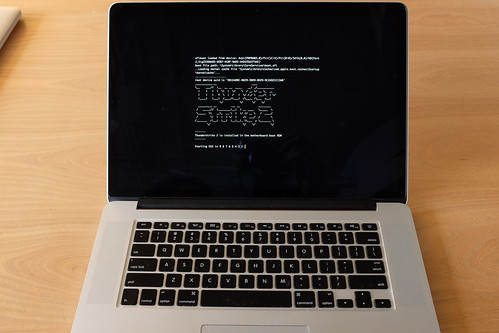
Trammell Hudson tests Apple macOS’s eficheck against Thunderstrike2:
https://twitter.com/qrs/status/927565241449410560
https://twitter.com/qrs/status/927599689515626496
https://trmm.net/Thunderstrike
https://trmm.net/Thunderstrike_2
https://support.apple.com/en-us/HT207475
https://twitter.com/osxreverser/status/912014988608491520
High Sierra automatically checks EFI firmware each week
Upgrading to High Sierra brings a new and significant security feature: your Mac will automatically check its EFI firmware. In a series of tweets, Xeno Kovah, one of the three engineers responsible for the new tool, has outlined how this works.[…]
AFAICT, the article references Tweets from earlier today that appear to have subsequently been deleted from Twitter.
Apple has apparently created a tool for examining Apple Mac EFI firmware, called eficheck. As I understand things, it was released, then pulled due to some issues (bugs?), and is apparently now avabilable in latest macOS updates. Also, it sounds like there might be another tool for NVMe diagnostics.
https://twitter.com/al3xtjames/status/874764154745368576
usage: eficheck: [–save -b] [ –cleanup -b] [–generate-hashes [-b] [-p]] [–integrity-check [-h [-b]]] [–show-hashes [-h] | [-b]]
https://www.apple.com/macos/sierra/
https://en.wikipedia.org/wiki/MacOS_High_Sierra
https://www.macrumors.com/roundup/macos-10-13/
Maybe someday there’ll be more info on eficheck, if you find any manpage or other info, please leave a Comment.
https://www.apple.com/us/search/eficheck
https://twitter.com/search?q=eficheck&src=typd
Mac Observer has an article about Apple’s Firmware Password security feature:
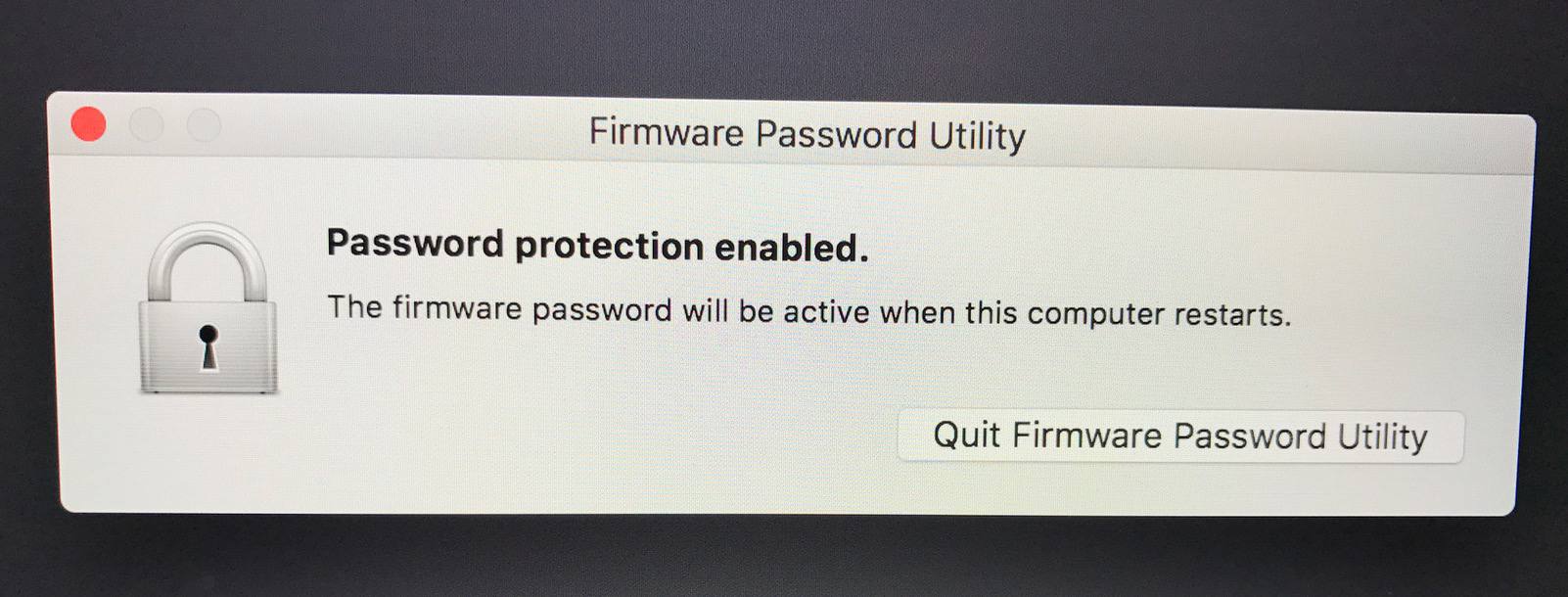
https://twitter.com/macOS_adm/status/889901131316559872
https://twitter.com/Contains_ENG/status/889878399195459589
On June 19th, Apple released a document describing how loading secure kernel extensions (.kext) would change with High Sierra and how this would impact enterprise customers.[…]
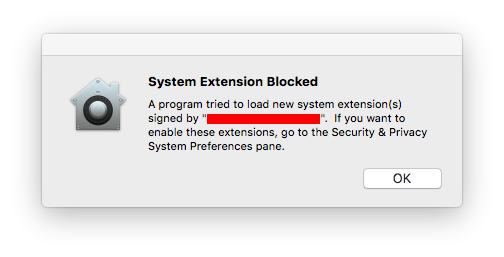
http://blog.eriknicolasgomez.com/2017/07/25/Kextpocalypse-High-Sierra-and-kexts-in-the-Enterprise/
https://developer.apple.com/library/content/technotes/tn2459/_index.html
http://newosxbook.com/2ndUpdate.html
In addition to update of Vol1, I just noticed there’s a Volume 3 on security:
http://newosxbook.com/toc3.html
Setup EFI Development environment on Mac OSX Sierra (10.12.X)
Mikal Villa Mikal Villa • 07/10/2017
Oh no! a lot of text. Well, luckly half of the post is troubleshooting. EFI development setup is easy 🙂
Okay, before starting this guide you should have some tools installed already.[…]
https://0xcc.re/setup-efi-development-environment-on-mac-osx-sierra-10-12-x/
If you are have an Apple system, here’s a guide to hardening macOS. Unlike most hardening guides, this one covers some aspects of firmware. I wish each OS vendor maintained a document like this.
https://github.com/drduh/macOS-Security-and-Privacy-Guide#firmware
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Discover the Desktop
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
News from coreboot world
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Just another WordPress.com site
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
You must be logged in to post a comment.