Sr. Hardware Security Engineer
AWS Security is looking for an experienced Senior Security Engineer, specializing in hardware technologies, to help ensure AWS services are designed and implemented to the highest possible security standards. You will be responsible for supporting AWS service teams in the secure design of services, including customer-facing services with hardware components such as AWS Snowball. As the primary technical and strategic advocate for a variety of AWS-wide security initiatives, you will help internal and external partners to design from the beginning with security in mind.This is not an entry-level position, and a confident understanding of hardware/firmware security and the ability to collaborate with other leaders across the industry are essential to success in this role.
[…]
* Demonstrate *exceptional* judgment, integrity, business acumen, and communication skills
* Minimum 4 years of experience with two or more of the following categories:
— IoT network technologies (Z-Wave, Zigbee, Bluetooth/BLE, WLAN, identity/auth security)
— Hardware security (PCB, JTAG, UART, SPI, ROM, microcode, custom ASIC/FPGA)
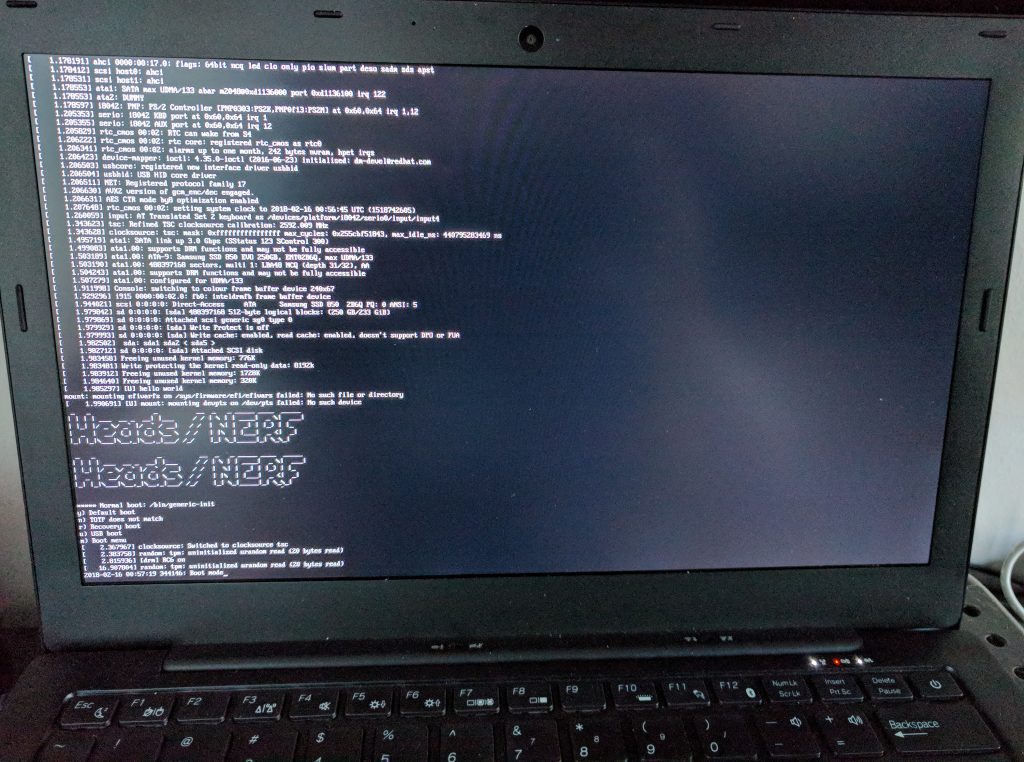
— x86 and/or ARM chipset and firmware security (TPM, UEFI, TrustZone, secure boot)
— Local encryption and key management (LUKS, BitLocker, self-encrypting drives, etc)
— PKI and code signing architecture (X.509, EV SSL, certificate pinning, OCSP, CRL, etc)
https://us-amazon.icims.com/jobs/626253/sr.-hardware-security-engineer/job
See-also:
AWS Snowball:
https://aws.amazon.com/snowball/



You must be logged in to post a comment.