http://decentsecurity.com/#/securing-your-computer/
There’s a new guide to securing Windows systems. I enjoyed it because step 2 of the steps are firmware-centric, excerpted below, view the original doc, the excerpted formatting is a bit mangled, sorry.
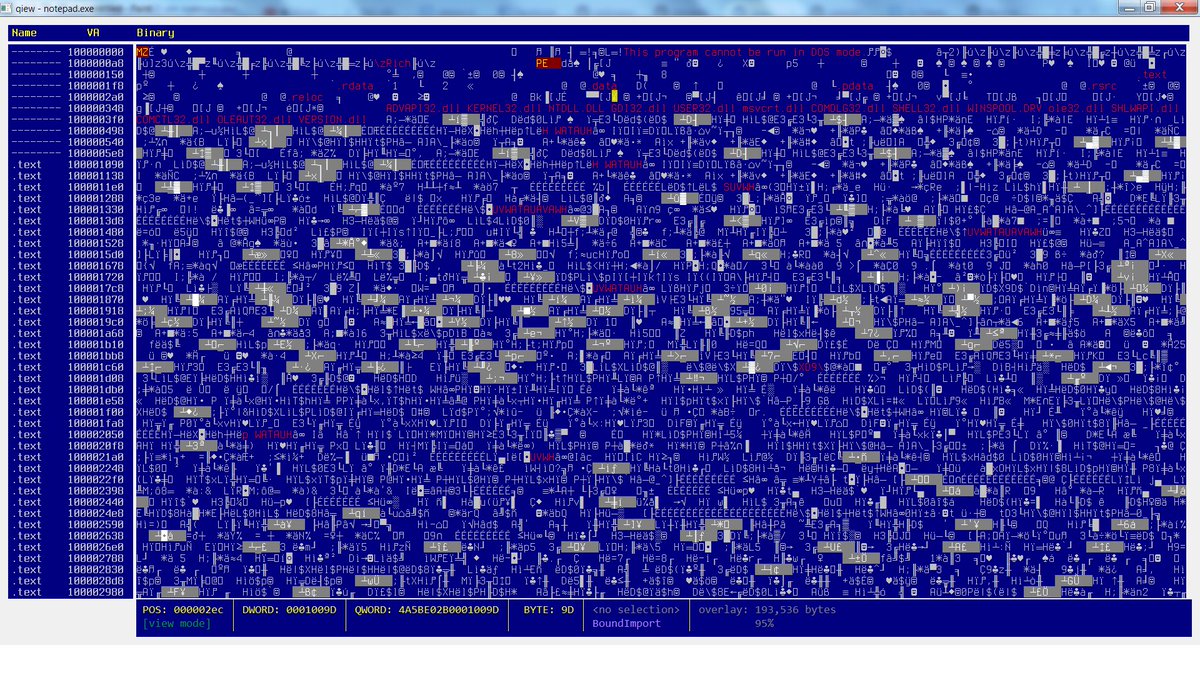
I wish the advice mentioned using CHIPSEC to do security tests to see if system came from OEM with unfixable security flaws, and to use CHIPSEC or other tools — perhaps via LUV-live or directly — to save a NIST SP-147-style ‘golden image’ of your ROM, doing periodic offline/forensic examination of your ROM images with CHIPSEC, UEFI Firmware Parser, and other tools. (I have no input as to the non-firmware Windows-centric input in the list.)
—
1.) Update BIOS
For best compatibility and security you should update your computer’s BIOS. A modern BIOS (really UEFI) is a full operating system that runs below and at the same time as Windows, and it needs patches too. People who built computers in the early 2000’s will tell you BIOS updates are risky, and they were, but not anymore. They deliver fixes, features, and security updates you won’t hear about on the news. Even new computers/motherboards need updates. If you’re starting from scratch, do the BIOS update after installing Windows 10. You can find the BIOS update tool on your manufacturer’s driver page for your computer model. You will need to reboot for it to take effect. If you have a Surface, BIOS updates are delivered through Windows Update.
—
3.) Configure BIOS
This is important and is something nobody talks about. From the boot of your computer, press the setup hotkey. It may be F1, F2, F8, F10, Del, or something else to get into SETUP mode. In the BIOS: Set a setup password. Make it simple, this is only to prevent malicious modification by someone in front of the computer or by a program trying to corrupt it. Change boot to/prioritize UEFI. Disable everything except UEFI DVD, UEFI HDD, and USB UEFI if you plan on using a USB stick to install Windows. Enable the TPM (if available) and SecureBoot (if available) options. This is super important. Disable 1394 (FireWire) and ExpressCard/PCMCIA (if you’re on a laptop) as a layer to further mitigate DMA attacks. This isn’t as important anymore, but if you don’t use them you might as well turn it off. If you want, and if the computer offers it, you can enable a System and HDD password. We will be using BitLocker to protect the disk, but this is an extra layer you can add if you want. I don’t. If you don’t use webcam or microphone, you may be able to turn them off in the BIOS. Save settings and shut down.
—
The Linux Foundation has some UEFI-centric, Linux-centric desktop advice, which has some overlaps in security methods to the above UEFI-centric, Windows-centric desktop advice:
Linux Foundation IT Security Policies: firmware guidance
The Crypto Party Handbook also has some related advice, for security/privacy-minded use. The Secure Desktop mailing list is the center of the universe for this, where the handful of Linux distributions that focus on secure/privacy as their main features, hang out. If you care about a secure OS, you should be using one of theirs, not an OS where security is not their primary concern.
https://github.com/cryptoparty/handbook
https://secure-os.org/pipermail/desktops/2015-October/000000.html
https://secure-os.org/desktops/charter/
[I need to find some similar security hardening checklist for ChomeOS-based, coreboot-based systems, instead of Windows-based UEFI/BIOS-based systems, talking about ensuring TPM on x86/x64, using coreboot with Verified Boot, specifics on how to best adopt those keys, like how Nikolaj shows us how to adopt UEFI Secure Boot keys, and others show how to use MOK. Any tips appreciated, please leave a Comment (see left) or send email (see above right). Thanks.]


You must be logged in to post a comment.