https://itpeernetwork.intel.com/intel-processors-fpga-better-together/

A quick and dirty tool written in C to split UEFI/BIOS files into two or more binary chunks, which can then be flashed onto a chip using flashrom or something similar. This was born out of the necessity of needing a UEFI and an EC (embedded controller) image to be reflashed manually on a laptop where the UEFI was 2MB and the EC was 128K, but seperate images were not available.
printf(“romsplit – split binary files into two or more seperate chunks\n”);
printf(“Usage: %s <filename> <size of chunk 1> <size of chunk 2> … <size of chunk n>\n\n”, argv[0]);
printf(“You must specify a filename and at least two chunk sizes\n”);
I think this web page by ARM Ltd is new, or at least updated:
https://developer.arm.com/technologies/uefi-drivers
Conclusion: Never trust USB devices (and not only storage devices…)
https://blog.rootshell.be/2018/05/22/evil-mouse-project/

DMTF Redfish has updated their schema and specs.
New Redfish Schema, Specification and Developer Resources Now Available. New items just released include:
* 2018.1 Redfish Schema Bundle: A .zip file that contains the current versions of all Redfish schema, including a new ExternalAccountProvider schema for LDAP/ActiveDirectory support. Additional schema updates enable support for Server Sent-Eventing (SSE), provide additional information for Processors and Settings, and more.
* Redfish Specification v1.5.0: Adds new support for SSE, enabling the streaming of events to web-based GUIs and other clients. Other specification updates in this release include a mechanism for specifying deterministic behavior for the application of Create, Delete or Action (POST) operations.
* Redfish Resource and Schema Guide: New for 2018, this human-readable guide to the Redfish Schema is designed to help educate users of Redfish. Application developers and DevOps personnel creating client-side software to communicate with a Redfish service, as well as other consumers of the API, will benefit from the explanations in this resource.
* Redfish 2018.1 Overview: Provides detailed descriptions of each revision in the latest version of the Redfish Schema and Specification.
https://www.dmtf.org/sites/default/files/standards/documents/DSP8010_2018.1.zip
Click to access DSP0266_1.5.0.pdf
Click to access DSP2046_2018.1_0.pdf
Click to access Redfish_2018_Release_1_Overview.pdf
http://redfish.dmtf.org/
http://www.dmtf.org/standards/redfish
KVM Forum 2018: Call For Participation
October 24-26, 2018
Edinburgh, UK
KVM Forum is an annual event that presents a rare opportunity for developers and users to meet, discuss the state of Linux virtualization technology, and plan for the challenges ahead. We invite you to lead part of the discussion by submitting a speaking proposal for KVM Forum 2018. […] This year, KVM Forum is joining Open Source Summit in Edinburgh, UK. Selected talks from KVM Forum will be presented on Wednesday October 24 to the full audience of the Open Source Summit. Also, attendees of KVM Forum will have access to all of the talks from Open Source Summit on Wednesday.[…]
https://events.linuxfoundation.org/events/kvm-forum-2018/program/cfp/
http://www.linux-kvm.org/page/KVM_Forum_2018_BOF
https://events.linuxfoundation.org/events/kvm-forum-2018/
https://mail.coreboot.org/pipermail/seabios/2018-May/012272.html
“This bug deserves more attention than it is currently receiving. It should be pinned in every forum with an affected machine, so that owners of those machines will be aware that it exists. It is currently squirreled away in the T series forum, under the outdated title “T480s – ACPI bug”. I have asked that the title be updated and received no response, which is why I’m posting this here.[…]
There’s a bug in the ACPI tables that affects all of the machines listed in the title. The bug causes heavy CPU usage on one thread due to frequent ACPI interrupts. The symptoms are a slow system, and high CPU temperatures (idles around 65 degrees Celsius). Some operating systems may mitigate the symptoms, but the bug is present regardless.
The following circumstances trigger it:
-powering on the laptop
-waking from suspend (and possibly hibernate – untested)
The following actions prevent it:
-reboot the laptop (temporary fix)
-disable thunderbolt in the UEFI settings (permanent fix – with latest UEFI updates)
The official UEFI update changelogs for all of these machines make explicit mention of this issue: “-(Fix) Fix an issue where system may become hot by system interrupts when Thundrebolt is disabled in ThinkPad Setup – Security – I/O Port Access.”[…]
https://forums.lenovo.com/t5/ThinkPad-T400-T500-and-newer-T/T480s-ACPI-bug/m-p/4064963#M124889
https://forums.lenovo.com/t5/ThinkPad-T400-T500-and-newer-T/T480s-ACPI-bug/m-p/4067181#M124936
https://download.lenovo.com/pccbbs/mobiles/n22ur05w.txt
https://www.intel.com/content/www/us/en/security-center/advisory/intel-sa-00115.html
https://www.intel.com/content/www/us/en/security-center/advisory/intel-sa-00115.html
https://www.us-cert.gov/ncas/alerts/TA18-141A
https://www.us-cert.gov/ncas/alerts/TA18-004A
https://twitter.com/daniel_bilar/status/998861828087275520
https://twitter.com/aionescu/status/998675842724069376
Closing Keynote: Betraying the BIOS: Where are the limits of AV for modern UEFI Firmware?
Alex Matrosov
For UEFI firmware, the barbarians are at the gate — and the gate is open. On the one hand, well-intentioned researchers are increasingly active in the UEFI security space; on the other hand, so are attackers. Information about UEFI implants — by HackingTeam and state-sponsored actors alike — hints at the magnitude of the problem, but are these isolated incidents, or are they indicative of a more dire lapse in security? Just how breachable is the BIOS? In this presentation, I’ll explain UEFI security from the competing perspectives of attacker and defender. I’ll cover topics including how hardware vendors have left SMM and SPI flash memory wide open to rootkits; how UEFI rootkits work, how technologies such as Intel Boot Guard and BIOS Guard (and the separate Authenticated Code Module CPU) aim to kill them; and weaknesses in these protective technologies. There are few public details; most of this information has been extracted by reverse engineering.
[Hmm, are there missing posts on FPMurphy’s blog? I seem to recall more recent posts, but don’t see them now, and only see this February-era post (which I think may be news to me): ]
A UEFI Shell tool for the CPUID instruction:
https://github.com/fpmurphy/UEFI-Utilities-2018/blob/master/MyApps/Cpuid/Cpuid.c
https://blog.fpmurphy.com/2018/02/simple-cpuid-utility-for-uefi-shell.html
https://twitter.com/fdiskyou/status/998133894351343616
Practical Symbolic Execution and SATisfiability Module Theories (SMT) 101
May 19, 2018 • By rui
Finding bugs is hard, reverse engineering is hard. Constraint solvers are the heart of many program analysis techniques, and can aid Fuzzing, and software verification.
This post contains a few hands-on experiments with Z3, a high performance theorem prover developed at Microsoft Research by Leonardo de Moura and Nikolaj Bjorner. With KLEE, a Symbolic Execution Engine built on top of the LLVM compiler infrastructure developed by Cristian Cadar, Daniel Dunbar, and Dawson Engler. And, angr, a binary analysis framework developed by the Computer Security Lab at UC Santa Barbara and their associated CTF team, Shellphish.[…]
http://deniable.org/reversing/symbolic-execution
Tianocore includes UEFI developer tools for creating ‘blobs’. But it also includes one tool useful for security researchers to examine existing Firmware Volumes. It is an OS-present tool that works on Mac/Windows/Linux, not a UEFI Shell tool.
https://github.com/tianocore/edk2/blob/master/BaseTools/Source/C/VolInfo/VolInfo.c
https://github.com/tianocore/edk2/tree/master/BaseTools/Source/C/VolInfo
https://github.com/tianocore/tianocore.github.io/wiki/EDK-II-Tools-List
https://github.com/tianocore/edk2/tree/master/BaseTools/UserManuals
https://raw.githubusercontent.com/tianocore/edk2/master/BaseTools/UserManuals/VolInfo_Utility_Man_Page.rtf
https://edk2-docs.gitbooks.io/edk-ii-build-specification/content/v/release/1.27/2_design_discussion/22_uefipi_firmware_images.html
http://wiki.phoenix.com/wiki/index.php/EFI_FIRMWARE_VOLUME_HEADER
Usage: VolInfo [options] <input_file>
Display Tiano Firmware Volume FFS image information
-h, –help — Show this help message and exit
–version — Show program’s version number and exit
-d [DEBUG], –debug [DEBUG] — Output DEBUG statements, where DEBUG_LEVEL is 0 (min) – 9 (max)
-v, –verbose — Print informational statements
-q, –quiet — Returns the exit code, error messages will be displayed
-s, –silent — Returns only the exit code; informational and errorvmessages are not displayed
-x XREF_FILENAME, –xref XREF_FILENAME — Parse the basename to file-guid cross reference file(s)
-f OFFSET, –offset OFFSET — The offset from the start of the input file to start processing an FV
–hash — Generate HASH value of the entire PE image
https://twitter.com/zackwhittaker/status/996758911989567488
https://news.ycombinator.com/item?id=17081684
https://www.qualcomm.com/products/izat
http://xt.qsp.qualcomm.com/privacy/privacy_policy.html
https://twitter.com/projectgus/status/996903073925623811
https://developer.qualcomm.com/comment/7260
https://copperhead.co/android/docs/usage_guide#default-connections-made-by-copperheados
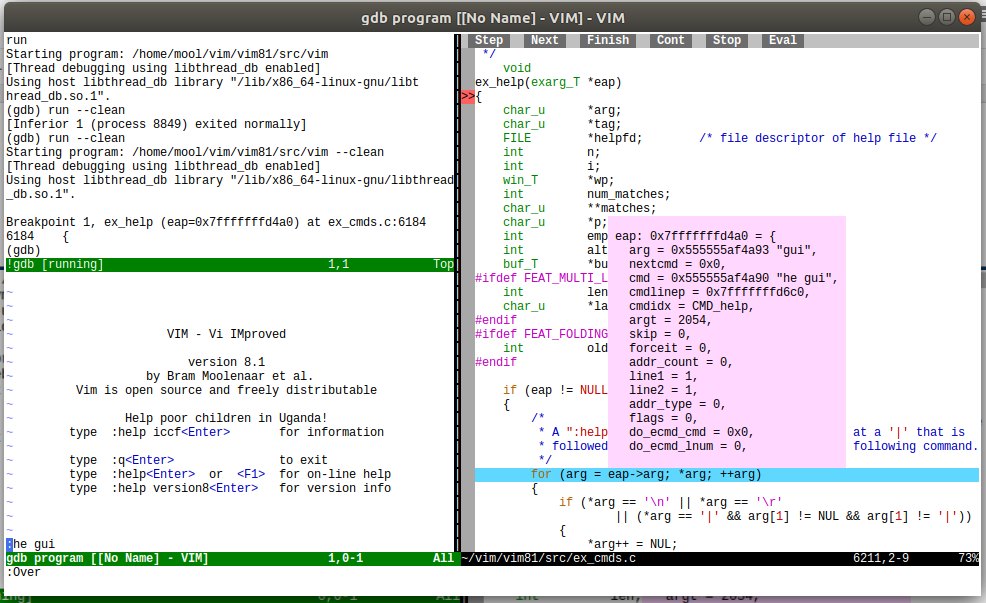
Fewer external plugins needed to use a shell within Vim anymore!
The main new feature of Vim 8.1 is support for running a terminal in a Vim window. This builds on top of the asynchronous features added in Vim 8.0. The terminal window can be used for many purposes, here are a few examples:
* Run a command, such as “make”, while continuing to edit in other windows. The progress of the command can be observed, the terminal window is continuously updated.
* Run a shell where you can execute a series of commands.
* Use the new terminal debugger plugin for debugging inside Vim. This is especially useful over an ssh connection, when opening other terminals is not possible or impractical. I use this to fix problems in Vim when travelling.
The terminal window is also used in tests, to grab a screenshot and compare it with the expected state. This allows for testing interactive actions, such as the popup menu.
https://www.vim.org/vim-8.1-released.php
The following changes have been made between LKRG 0.1 and 0.2:
*) Add support for being loaded at early boot stage (e.g. from initramfs)
*) [CI] Add a new sysctl to control whether LKRG performs code integrity checks on random events (or only at regular intervals)
*) Reduce performance impact, e.g. in our specific test case:
-> Average cost of running a fully enabled LKRG => 2.5%
-> Average cost of running LKRG without the code integrity checks on random events (disabled with the new sysctl) => 0.7%
*) [CI] Fix a potential deadlock bug caused by get_online_cpus() function, which might sleep if CONFIG_PREEMPT_VOLUNTARY=y
*) [CI] Fix dynamic NOPs injected by *_JUMP_LABEL for MWESTMERE
*) [CI] Remove false positives caused by *_JUMP_LABEL in corner case scenarios
*) [ED] Remove false positives when kernel executes usermode helper binaries
Legend:
[CI] – Code Integrity
[ED] – Exploit Detection
https://www.patreon.com/p_lkrg
http://www.openwall.com/lists/announce/2018/03/27/1

Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Discover the Desktop
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
News from coreboot world
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
Just another WordPress.com site
Hastily-written news/info on the firmware security/development communities, sorry for the typos.
You must be logged in to post a comment.