Priceonomics has a great new summary of cyberattacks over time:
Why Security Breaches Just Keep Getting Bigger and More Expensive
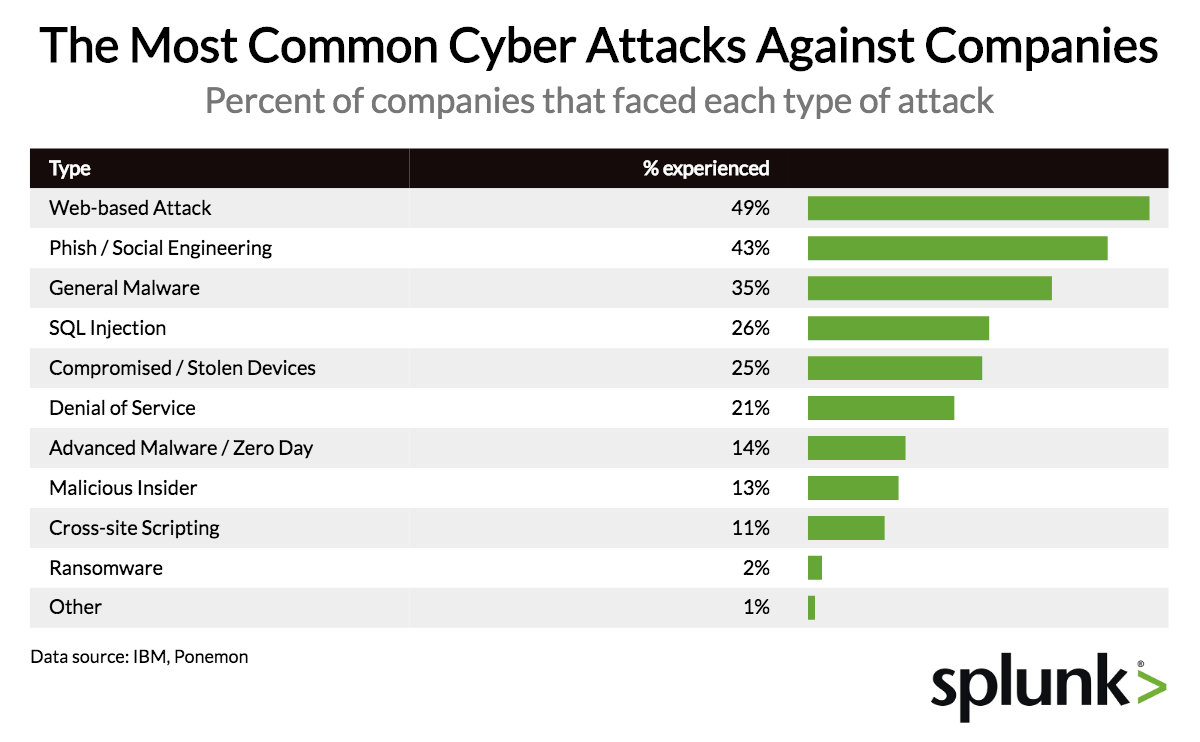
I’d like to draw your attention to just one chart – which I’ll embed below (link may break):
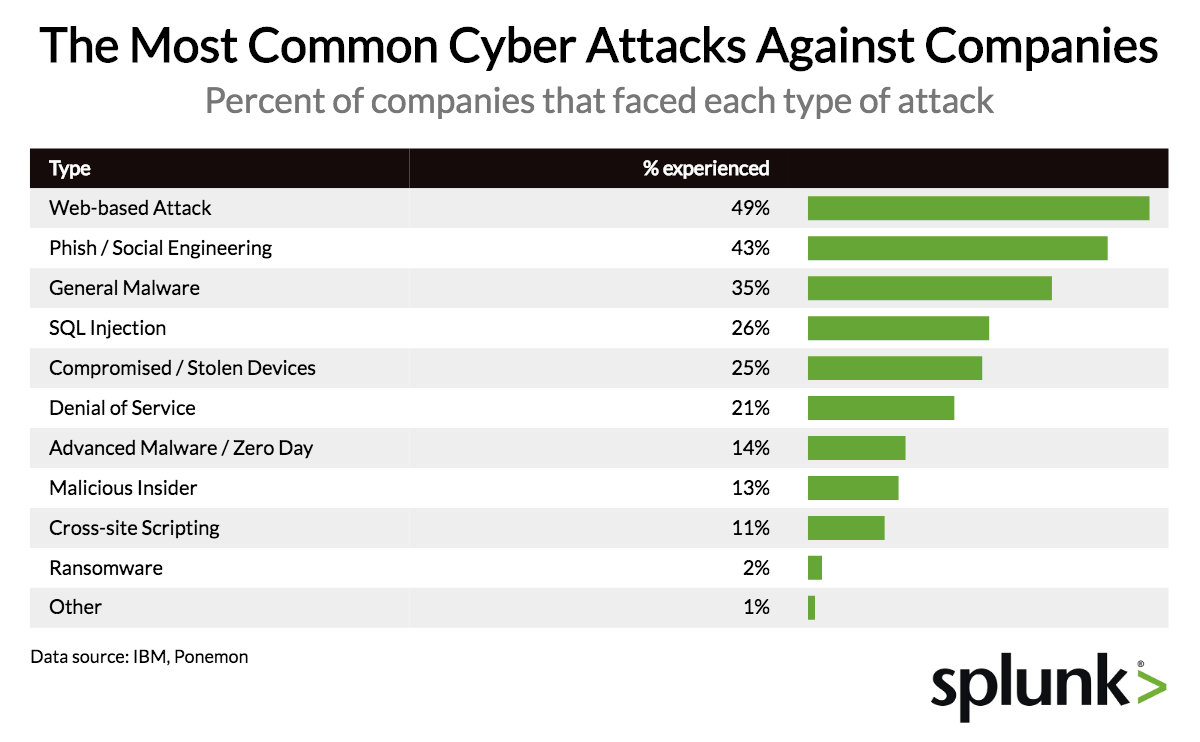
One might look at this and say that firmware is virtually irrelevant. Certainly the baseline security advice is to start with the the things that are the most likely and impactful. So – if something is likely, but the impact is low, or if something is unlikely but the impact is high.. deprioritize it.
Note that the total here is far greater than 100%.. so I guess they’re saying that successful attacks often involve multiple of these categories. eg: Phishing that gets you to click on a bogus link is also a web-based attack? I guess?
But consider that:
- For certain firmware is involved in EVERY attack in the “compromised / stolen devices” category, which represents 25%.
- If a device is compromised in this way, even if you have full disk encryption, a firmware or side-channel attack may work.
- Even if you get it back, the device cannot be trusted any longer
- Malicious insider threats should also be considered to possibly involve firmware. What physical devices has that person touched? Ever?
- Because the totals are > 100%, it is possible that firmware is involved in some of the other types of attacks as well – though I acknowledge that the percentage is probably low. Why attack firmware when you can execute a successful phishing attack?
- General Malware – if the firmware can be updated while the OS is running (typically with admin/root privs), then malicious firmware can be installed by any regular malware that gets admin.
While the probability is STILL low, it is worth looking at numbers like this and reading between the lines a bit. Some types of protection, such as Secure Boot are worth enabling, or rather, not disabling!
Every cross fleet operation can balloon into a huge effort, such as deploying and ensuring anti-virus is up to date. So how about firmware updates? Some are now delivered with OS updates via Windows Update and or fwupd on Linux. If you can’t afford the massive amount of labor to consistently ensure that all your machines have up-to-date firmware, AT A MINIMUM, shoot an email to your purchasing department, and pressure your sales engineer that ALL future systems you purchase get firmware updates for ALL OS-updatable firmware – not just UEFI/BIOS, via the OS update mechanisms. Signed, forward-only, please.

You must be logged in to post a comment.